Unlock your full potential by mastering the most common Cargo Inspection and Security interview questions. This blog offers a deep dive into the critical topics, ensuring you’re not only prepared to answer but to excel. With these insights, you’ll approach your interview with clarity and confidence.
Questions Asked in Cargo Inspection and Security Interview
Q 1. Describe your experience with various cargo inspection techniques.
Cargo inspection techniques vary widely depending on the type of cargo, destination, and potential risks. My experience encompasses a range of methods, from visual inspections and physical examinations to the use of advanced scanning technologies.
Visual Inspection: This is the first and often most crucial step. It involves carefully observing the cargo for any signs of tampering, damage, or inconsistencies with the shipping documentation. For example, I might look for unusual bulges, loose seals, or discrepancies between the declared contents and the packaging.
Physical Examination: This involves physically handling the cargo, opening containers or packages (if necessary and permitted), and examining the contents for prohibited or undeclared items. This could involve checking weight, measuring dimensions, or even taking samples for laboratory analysis. I have experience in meticulously documenting each step of this process.
Non-Intrusive Inspection (NII): Technologies like X-ray and gamma-ray scanning allow for the inspection of cargo without physically opening containers. I am proficient in interpreting the images produced by these scanners, identifying potential threats like hidden weapons or explosives. I’ll elaborate on this further in a later response.
K9 Detection: Utilizing trained dogs to detect narcotics, explosives, or other contraband is another valuable technique. I have collaborated with canine units on numerous occasions, and understand their limitations and strengths.
The choice of inspection technique is always risk-based, guided by intelligence and the specifics of each shipment.
Q 2. Explain the different types of cargo security threats.
Cargo security threats are diverse and constantly evolving. They can be broadly categorized as:
Terrorism and Weapons of Mass Destruction (WMD): This includes the smuggling of explosives, chemical, biological, or nuclear weapons, or components thereof. This is arguably the most significant threat, necessitating rigorous security protocols.
Narcotics and Illicit Drugs: The global drug trade poses a significant challenge, with smugglers constantly devising new methods to conceal and transport drugs.
Smuggling of Prohibited Goods: This encompasses a broad range of items, from counterfeit goods and stolen property to endangered species and illegal wildlife products.
Cybersecurity Threats: Targeting of supply chain systems through cyberattacks, aimed at manipulating shipping documents or gaining access to sensitive cargo information.
Theft and Pilferage: The unauthorized removal of cargo from containers or during transit, which can lead to significant financial losses.
Concealment of Dangerous Goods: Incorrectly declared or undeclared hazardous materials pose substantial risks to personnel and the environment. This necessitates proper labeling and documentation.
Understanding the evolving nature of these threats requires continuous learning and adaptation.
Q 3. How do you identify and handle suspicious cargo?
Identifying suspicious cargo relies on a combination of observation, analysis, and experience. Indicators can be subtle or overt. I would approach this systematically:
Risk Assessment: Evaluate the origin, destination, and contents of the shipment. High-risk routes and origins warrant more thorough inspections.
Documentation Review: Carefully examine all shipping documents for inconsistencies or discrepancies. Mismatches between the declared contents and the packaging can be a red flag.
Visual Inspection and Physical Examination: As previously described, I would meticulously examine the cargo, noting any unusual characteristics such as unexpected weight, unusual odors, or damage inconsistent with normal handling.
Scanning Technologies: Employing NII techniques helps to identify hidden objects or substances. Anomalies detected through scanning would prompt further investigation.
Intelligence and Information Sharing: Staying up-to-date on current smuggling trends and leveraging information from intelligence agencies or other security partners is crucial.
If suspicion remains, I would immediately escalate the matter to the appropriate authorities, following established protocols for handling suspicious cargo. This might include isolating the cargo, restricting access, and notifying relevant agencies (such as customs, border protection, and law enforcement).
Q 4. What are the key regulations and compliance requirements in cargo security?
Cargo security is governed by a complex web of international and national regulations. Key frameworks include:
International Ship and Port Facility Security (ISPS) Code: This sets minimum security standards for ships and port facilities worldwide. It mandates risk assessments, security plans, and security measures to mitigate threats.
Customs Regulations: Each country has specific regulations regarding the import and export of goods, including prohibited and restricted items. These regulations often specify documentation requirements and inspection procedures.
Container Security Initiative (CSI): This US-led initiative involves pre-screening containers at foreign ports to enhance security and efficiency.
Autonomous Sanctions: These are unilateral sanctions imposed by individual countries, targeting specific individuals, entities, or goods. They can impact cargo movement and necessitate meticulous compliance.
Compliance requires a thorough understanding of these regulations, continuous monitoring for updates, and robust internal security procedures. Failure to comply can result in severe penalties, including fines, delays, and legal repercussions.
Q 5. What are your methods for documenting cargo inspection findings?
Meticulous documentation is paramount in cargo inspection. My methods typically involve:
Detailed Inspection Reports: These reports document every aspect of the inspection, including the date, time, location, cargo details, inspection methods used, and any findings. They often include photographs or video recordings as supporting evidence.
Digital Imaging and Data Logging: Images from scanning technologies, along with data from other inspection tools, are digitally recorded and stored securely. This provides a tamper-proof audit trail.
Chain of Custody: Maintaining a clear chain of custody for any samples or seized items is crucial for legal purposes. This involves detailed records of handling, transfer, and storage.
Secure Data Storage: All inspection records are stored securely, complying with data protection regulations and access control policies.
The documentation serves as evidence for audits, investigations, and legal proceedings, ensuring accountability and transparency.
Q 6. Describe your experience with cargo scanning technologies (X-ray, gamma-ray).
I have extensive experience with both X-ray and gamma-ray scanning technologies. These non-intrusive inspection methods provide valuable insights into the contents of containers without the need to physically open them.
X-ray Scanning: Uses X-rays to create images of the cargo’s interior. Different materials absorb X-rays differently, allowing us to differentiate between various substances. I’m proficient in interpreting X-ray images, recognizing anomalies indicative of concealed contraband. For example, areas of unusual density might indicate the presence of metallic objects or dense materials.
Gamma-ray Scanning: This technology uses gamma rays, which have greater penetrating power than X-rays, allowing for the inspection of denser materials. Gamma-ray scanners are particularly useful for identifying high-density materials that may be difficult to detect with X-ray scanners.
The interpretation of these images requires specialized training and experience. I am adept at identifying suspicious objects or materials based on their density, shape, and location within the container. My skills extend to interpreting the various artifacts and noise in the scan to distinguish between false positives and potential threats.
Q 7. How would you respond to a security breach during cargo handling?
Responding to a security breach during cargo handling requires a swift and coordinated response. My approach would be:
Immediate Containment: Secure the area to prevent further access to the compromised cargo and minimize any potential spread of the threat.
Alert Authorities: Immediately notify relevant authorities such as port security, law enforcement, and potentially counter-terrorism units, depending on the nature of the breach.
Evidence Preservation: Preserve all evidence related to the breach, including any physical evidence, security footage, and inspection records. Maintain a clear chain of custody for any evidence collected.
Damage Assessment: Evaluate the extent of the breach and assess the potential impact. This includes identifying any missing or compromised goods, evaluating potential damage to infrastructure, and assessing potential risks to personnel and the environment.
Investigation and Reporting: Cooperate fully with the authorities’ investigation and provide all necessary documentation and information. This includes submitting detailed reports on the incident, including the timeline of events, identified threats, and any actions taken.
Post-Incident Review: Conduct a thorough post-incident review to identify weaknesses in existing security procedures, recommend corrective actions, and implement necessary improvements to prevent future breaches. This review should involve cross-functional teams including security personnel, operations management and technology.
The specific response will vary depending on the nature of the breach, but the principles of containment, immediate notification, evidence preservation, and thorough investigation remain consistent.
Q 8. Explain your understanding of the International Ship and Port Facility Security (ISPS) Code.
The International Ship and Port Facility Security (ISPS) Code is a mandatory international standard developed by the International Maritime Organization (IMO) to enhance maritime security. It aims to prevent acts of terrorism against ships and port facilities. Think of it as a comprehensive security manual for the maritime industry.
The ISPS Code mandates a layered security approach. This includes assigning a designated Security Officer responsible for implementing the Ship Security Plan (SSP) for ships and the Port Facility Security Plan (PFSP) for port facilities. These plans detail security measures tailored to the specific risks associated with each vessel and port.
Key aspects include:
- Security Assessments: Regular assessments to identify vulnerabilities and potential threats.
- Security Levels: The ability to adjust security measures based on the current threat level (e.g., heightened security during a geopolitical crisis).
- Communication Protocols: Clear communication channels between ships, port authorities, and other stakeholders.
- Access Control: Strict control over access to ships and port areas.
- Personnel Security: Background checks and security training for personnel involved in maritime operations.
For example, a ship arriving from a high-risk region might be subjected to a more rigorous inspection, including enhanced security checks of crew and cargo, reflecting the elevated security level.
Q 9. How do you ensure the integrity of the cargo inspection process?
Ensuring the integrity of the cargo inspection process requires a multi-faceted approach. It’s like building a strong chain; each link must be secure.
- Independent Verification: Using multiple inspectors or independent verification teams to cross-check findings and reduce the risk of errors or omissions.
- Technological Aids: Utilizing technologies like X-ray scanners, gamma-ray detectors, and other non-intrusive inspection techniques to detect concealed contraband or dangerous goods.
- Chain of Custody: Maintaining a meticulous record of every step, including who handled the cargo, where it was inspected, and any anomalies detected. This creates an auditable trail.
- Proper Documentation: Detailed inspection reports with photos, video evidence, and signatures from involved parties ensure accuracy and transparency.
- Seals and Lock Verification: Checking the integrity of seals and locking devices on containers to ensure that they haven’t been tampered with during transit.
- Training and Certification: Inspectors must be trained, competent, and certified, following strict protocols and guidelines.
For instance, if a discrepancy is found between the manifest and the physical cargo, a thorough investigation is immediately initiated, involving potentially the relevant customs authorities.
Q 10. What is your experience with different types of cargo containers and their security features?
My experience encompasses a wide range of container types, each with its own security features. These include:
- Standard Dry Containers: These are the most common and offer basic security through locking mechanisms and seals. However, their vulnerability to tampering is well-known.
- Refrigerated Containers (Reefer Containers): These containers maintain temperature control and are often used for perishable goods. Security is similar to dry containers, but the refrigeration unit itself can also be a target for tampering.
- Tank Containers: Used for liquid cargo, tank containers have specialized locking mechanisms and are often monitored remotely via GPS tracking and telemetry systems.
- Open-Top Containers: These lack a top cover, increasing vulnerability to theft and environmental damage. Securement measures are crucial here, such as tarpaulins and additional seals.
- High-Cube Containers: These offer increased volume and present similar security challenges to standard containers.
Modern containers often incorporate advanced security features such as GPS tracking, electronic seals that provide tamper alerts, and reinforced locking mechanisms.
Q 11. How do you assess the risk level of different shipments?
Risk assessment of shipments involves a combination of factors and employs a structured approach. It’s similar to conducting a thorough risk analysis of any major project.
- Origin and Destination: Shipments originating from or destined for high-risk regions automatically elevate the risk level.
- Cargo Type: Certain goods (e.g., narcotics, weapons, hazardous materials) inherently pose higher risk.
- Shipper and Consignee: The reputation and past behavior of the shipper and consignee are assessed.
- Transportation Route: Routes traversing unstable or conflict zones increase risk.
- Mode of Transport: Certain transport modes (e.g., less secure roads) are more prone to security breaches.
- Historical Data: Analyzing past security incidents involving similar shipments can inform risk profiles.
A scoring system or matrix is typically used to quantify the identified risks, resulting in a final risk level that determines the intensity and type of inspections.
Q 12. Describe your experience with cargo manifest verification.
Cargo manifest verification is a critical step in the security process. It’s like double-checking the ingredients before baking a cake; you want to ensure you’re using what you think you’re using.
I have extensive experience verifying cargo manifests against physical cargo inspections. This involves comparing the declared contents and quantities in the manifest with the actual contents and quantities of cargo. Inconsistencies trigger an immediate investigation, potentially involving further inspections, including non-intrusive inspection techniques.
Discrepancies can involve missing items, substitution of goods, or undeclared hazardous materials. The process relies heavily on detailed documentation and precise identification of cargo items. We follow established procedures to escalate discrepancies to the appropriate authorities.
Q 13. How familiar are you with the use of seals and locking devices?
Seals and locking devices are fundamental to cargo security. They act as the first line of defense against tampering. Think of them as the locks on your house door – a deterrent against unauthorized entry.
I am highly familiar with various types of seals, including bolt seals, lead seals, and high-security seals with unique identification numbers. I also have experience with electronic seals, which offer advanced tamper-detection capabilities through integrated sensors and data logging. The verification process involves visually inspecting seals for signs of tampering, checking their integrity, and confirming that the seals match the information on the documentation.
Knowledge of the different types of seals and locking mechanisms is essential to determining the level of security provided, particularly in high-risk scenarios.
Q 14. What is your experience with reporting procedures for security incidents?
Reporting procedures for security incidents are critical for maintaining the safety and security of the supply chain. These procedures must be prompt, accurate, and follow established protocols.
My experience includes reporting incidents ranging from minor damage to containers to major security breaches, including theft, smuggling, and potential acts of terrorism. I am familiar with all relevant reporting protocols and regulatory requirements. Reports typically contain detailed descriptions of the event, evidence collected, and actions taken. These reports are often submitted to various authorities, including port authorities, customs officials, and relevant law enforcement agencies.
Timely and accurate reporting is crucial for initiating investigations, preventing future incidents, and improving overall security measures.
Q 15. Explain your understanding of customs procedures and regulations.
Customs procedures and regulations are the rules and processes governing the import and export of goods across international borders. They aim to control the flow of goods, protect national security, collect revenue (through duties and taxes), and ensure compliance with various trade agreements and national laws. These procedures vary significantly depending on the country, the type of goods being transported, and the involved parties.
For instance, understanding the Harmonized System (HS) codes is crucial. These six-digit codes classify goods internationally, determining applicable tariffs and regulations. A misclassified item can lead to significant delays and penalties. Other key aspects include documentation (e.g., commercial invoices, packing lists, certificates of origin), inspections (physical examinations, document reviews), and the payment of duties and taxes.
In practice, I’ve encountered situations where incorrect documentation led to cargo being held up at customs. Identifying the missing or incorrect information, quickly rectifying it, and working with customs officials to ensure a swift release requires a thorough understanding of procedures and excellent communication skills.
- Documentation review: Ensuring all necessary paperwork is accurate and complete is paramount.
- Tariff classification: Correctly identifying HS codes to ensure accurate duty calculation.
- Compliance verification: Checking for compliance with any specific regulations related to the cargo (e.g., permits, licenses).
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. How do you maintain a secure working environment?
Maintaining a secure working environment in cargo inspection involves a multi-layered approach. This begins with robust physical security measures like access control systems (e.g., keycard access, CCTV surveillance), secure storage facilities for sensitive equipment, and well-lit inspection areas to deter unauthorized access or activity. But physical security is only one part of the equation.
Equally important is procedural security. This includes strict adherence to protocols for handling sensitive information (e.g., proper disposal of confidential documents), secure data storage practices (encrypted databases and access controls), and regular security awareness training for all personnel. We also conduct background checks and security vetting of all personnel to ensure the highest integrity and trustworthiness. In one instance, we strengthened our security by implementing a two-person rule for all high-risk inspections, eliminating any chance of individual compromise.
Finally, maintaining a strong culture of security and reporting is critical. Employees are encouraged to report any suspicious activity, and a system is in place to investigate and address such concerns promptly. This creates an environment where everyone is responsible for and contributes to the overall security posture.
Q 17. Describe your problem-solving skills in relation to a cargo security issue.
Problem-solving in cargo security often involves a structured approach. For example, I once encountered a situation where a container’s seal was compromised, raising suspicion of tampering. My systematic approach involved these steps:
- Assessment: The initial step was to secure the container and assess the extent of the damage. Photographs and detailed notes were documented.
- Investigation: I investigated the container’s journey, reviewing its history, examining the manifest, and contacting relevant parties (shipping lines, customs officials).
- Evidence gathering: Collecting evidence, including the compromised seal, any signs of forced entry, and potential fingerprints or traces of tampering.
- Analysis: Reviewing the collected evidence helped me determine the probable cause and the potential impact.
- Solution development: Based on the analysis, I worked with customs authorities to implement corrective actions (e.g., a more thorough inspection, additional security measures).
- Communication: Effective communication was vital to keep all stakeholders informed and coordinated throughout the process.
This case highlighted the importance of a structured, investigative approach when dealing with cargo security breaches.
Q 18. How familiar are you with different types of cargo security equipment?
I am very familiar with a range of cargo security equipment. This includes:
- Radiation detection equipment: Used to detect nuclear and radioactive materials, such as portal monitors and handheld radiation detectors.
- Explosives detection equipment: Employing various technologies (e.g., ion mobility spectrometry, trace detection) to identify explosive materials.
- X-ray inspection systems: Providing non-invasive imaging of cargo containers to identify concealed items or anomalies.
- Container seals and locks: Ensuring the integrity of containers and preventing unauthorized access.
- GPS tracking devices: Monitoring the location and movement of cargo during transit.
My experience extends to operating and maintaining several types of this equipment, understanding their limitations, and interpreting their results. Proper training and certification are essential for safe and accurate usage of these technologies.
Q 19. What experience do you have with using handheld inspection devices?
I possess extensive experience using various handheld inspection devices, including:
- Handheld radiation detectors: I’m proficient in operating these devices, interpreting readings, and recognizing potential radiation threats.
- Portable narcotics and explosives detectors: Experienced in using these devices to detect trace amounts of illicit substances on surfaces.
- Metal detectors: Competent in using both handheld and walk-through metal detectors to screen personnel and cargo.
Regular training and calibration ensure accurate readings and reliable results. I understand the limitations of these devices and know when to use them in conjunction with other inspection methods for a comprehensive approach.
Q 20. How do you prioritize tasks during a high-volume cargo inspection?
Prioritizing tasks during high-volume cargo inspections requires a systematic approach. I use a risk-based prioritization method, focusing on containers and cargo that pose the highest risk based on several factors:
- Origin and destination: High-risk regions are prioritized for enhanced scrutiny.
- Cargo type: Certain types of goods (e.g., high-value electronics, controlled substances) warrant closer inspection.
- Shipper and consignee history: Prior history of non-compliance or suspicious activity influences prioritization.
- Container condition: Signs of tampering or damage trigger immediate attention.
This risk-based approach, coupled with efficient workflow management and clear communication among the inspection team, ensures that resources are allocated effectively. Time-sensitive cargo is also given appropriate priority while maintaining thoroughness in all inspections.
Q 21. What measures do you take to ensure the accuracy of your inspections?
Ensuring accuracy in cargo inspections relies on a combination of factors:
- Proper training and certification: All personnel undergo rigorous training on inspection procedures and the use of inspection equipment.
- Standard operating procedures (SOPs): Strict adherence to SOPs ensures consistency and minimizes human error.
- Calibration and maintenance: All inspection equipment is regularly calibrated and maintained to ensure accuracy and reliability.
- Quality control measures: Regular audits and inspections of our procedures help identify areas for improvement.
- Documentation and record-keeping: Meticulous record-keeping provides a verifiable audit trail of every inspection.
- Cross-checking and verification: Multiple inspectors may review high-risk cargo to enhance accuracy.
Continuous improvement is a central aspect of our process, always looking for ways to enhance accuracy and efficiency, and to ensure our compliance with all applicable regulations.
Q 22. Describe your experience with internal and external audits related to cargo security.
Internal and external audits are crucial for maintaining robust cargo security. Internal audits involve self-assessment of our security protocols, identifying weaknesses, and implementing corrective actions. Think of it like a personal health check-up for your security system. We review our procedures, document compliance, and look for vulnerabilities. External audits, on the other hand, are conducted by independent third-party organizations, providing an objective evaluation of our security posture. This is like having a specialist review your health – they bring fresh eyes and expertise to identify areas for improvement.
For example, during an internal audit, we might analyze our container-tracking system for any gaps in data logging or identify procedural inconsistencies in our security checks. An external audit might involve a physical inspection of our facilities and a review of our employee training records against industry best practices. Both types of audits provide valuable insights to help us strengthen our cargo security measures and ensure we meet regulatory compliance standards.
Q 23. How do you stay up to date on changes in cargo security regulations?
Staying current with the ever-evolving landscape of cargo security regulations requires a multi-pronged approach. Firstly, I actively subscribe to and monitor newsletters and publications from organizations like the International Maritime Organization (IMO), the Transportation Security Administration (TSA), and other relevant governmental bodies. This keeps me abreast of any new regulations, amendments, or security alerts. Secondly, I regularly attend industry conferences and webinars; these events offer valuable networking opportunities and provide insights into the latest security technologies and best practices. Thirdly, I maintain professional memberships in organizations focused on cargo security, providing access to exclusive resources, updates, and industry experts.
Imagine it’s like subscribing to several newspapers to stay informed about different perspectives. By combining these approaches, I ensure that I have a comprehensive and up-to-date understanding of all relevant regulations, thereby mitigating potential risks and maintaining the highest security standards.
Q 24. Describe a time you had to make a difficult decision regarding cargo security.
During a shipment of high-value electronics, we received intelligence suggesting a potential internal threat. A difficult decision arose regarding whether to initiate a full-scale investigation, potentially disrupting operations and damaging employee morale, or to proceed with caution and potentially risk compromise. We chose a phased approach, initiating a discreet internal audit focused on access controls and personnel background checks while simultaneously enhancing surveillance measures. This allowed us to address the threat without causing undue alarm or disruption. Fortunately, the investigation uncovered a minor procedural lapse, which we addressed immediately, preventing a potentially serious security breach. The key was balancing risk mitigation with maintaining operational efficiency and employee trust.
Q 25. Explain your experience with different types of cargo security technologies.
My experience encompasses a wide range of cargo security technologies. This includes GPS tracking devices for real-time monitoring of shipments, RFID (Radio-Frequency Identification) tags for asset identification and tracking, and various forms of tamper-evident seals to detect unauthorized access. I’m also familiar with advanced technologies such as container scanning systems using X-ray or gamma rays for non-intrusive inspection and video surveillance systems integrated with AI-powered analytics for threat detection.
For instance, we use GPS tracking on high-risk shipments to monitor their location and movement in real-time, alerting us to any deviations from the planned route. RFID tags help us track individual containers within a larger shipment, improving inventory management and preventing loss. The integration of these technologies has significantly improved our ability to detect and prevent cargo theft and security breaches.
Q 26. How do you collaborate with other team members to ensure cargo security?
Effective collaboration is paramount in cargo security. I foster a team environment where open communication and information sharing are prioritized. We utilize regular team meetings to discuss potential risks, share intelligence, and coordinate security measures. We use collaborative software platforms to track shipments, share updates, and manage alerts. Clear roles and responsibilities are defined to ensure accountability and efficient teamwork. This collaborative approach ensures that all team members are informed, engaged, and working together to achieve the common goal of securing our cargo.
Imagine a well-orchestrated orchestra – each musician has a specific role, but the success of the performance depends on seamless coordination and communication between all players.
Q 27. What is your experience with investigating cargo theft or loss?
Investigating cargo theft or loss involves a systematic and meticulous approach. It starts with gathering all available information – including shipment manifests, tracking data, security footage, and witness statements. Next, we analyze this information to identify potential points of failure or suspicious activity. This might involve reviewing security camera footage, analyzing GPS data for route deviations, or interviewing personnel who handled the shipment. The investigation might also involve collaborating with law enforcement agencies to track stolen goods or pursue legal action against those responsible.
In one instance, we traced a stolen shipment using GPS data and security camera footage, leading to the recovery of the cargo and the apprehension of the perpetrators.
Q 28. Describe your experience with training others in cargo security procedures.
Training is crucial for maintaining high security standards. I develop and deliver training programs that cover a range of topics, including cargo security procedures, threat awareness, and the use of security technologies. The training incorporates practical exercises and scenarios to enhance learning and retention. For instance, we conduct regular drills simulating different security threats, allowing personnel to practice their responses in a safe and controlled environment. I also tailor the training to specific roles and responsibilities within the team, ensuring that everyone is adequately trained to perform their duties effectively. I regularly evaluate the effectiveness of the training programs and make adjustments to ensure that they remain current and relevant.
Think of it as teaching a life-saving skill – clear, consistent, and practical training is absolutely essential for maintaining optimal performance in high-pressure situations.
Key Topics to Learn for Cargo Inspection and Security Interview
- International Regulations and Conventions: Understanding key international regulations like the ISPS Code, customs regulations, and relevant conventions is crucial for ensuring compliance and security. Practical application includes knowing how these regulations impact specific inspection procedures.
- Cargo Scanning and Detection Technologies: Familiarize yourself with various non-intrusive inspection (NII) technologies like X-ray, gamma-ray, and millimeter-wave scanners. Practical application includes understanding the limitations and strengths of each technology and how to interpret scan images effectively.
- Risk Assessment and Threat Analysis: Learn to identify high-risk cargo, potential threats, and vulnerabilities in the supply chain. Practical application includes applying risk assessment methodologies to prioritize inspections and allocate resources effectively.
- Container Security and Sealing Techniques: Understand the importance of proper container sealing and security measures to prevent tampering and theft. Practical application includes recognizing different types of seals and knowing how to verify their integrity.
- Dangerous Goods Identification and Handling: Master the identification and handling procedures for hazardous materials according to the relevant regulations (e.g., IMDG Code). Practical application includes recognizing hazard labels, understanding safety protocols, and reporting procedures.
- Reporting and Documentation Procedures: Understand the importance of accurate and timely reporting. Practical application includes knowing the proper format and procedures for documenting inspections, findings, and security incidents.
- Physical Inspection Techniques: Develop proficiency in conducting thorough physical inspections of cargo, containers, and vehicles. Practical application includes knowing how to systematically search for contraband and irregularities.
- Security Technologies and Systems: Understand various security systems used in ports and terminals, including access control, CCTV, and alarm systems. Practical application includes understanding how these systems contribute to overall security and how to respond to alarms or security breaches.
Next Steps
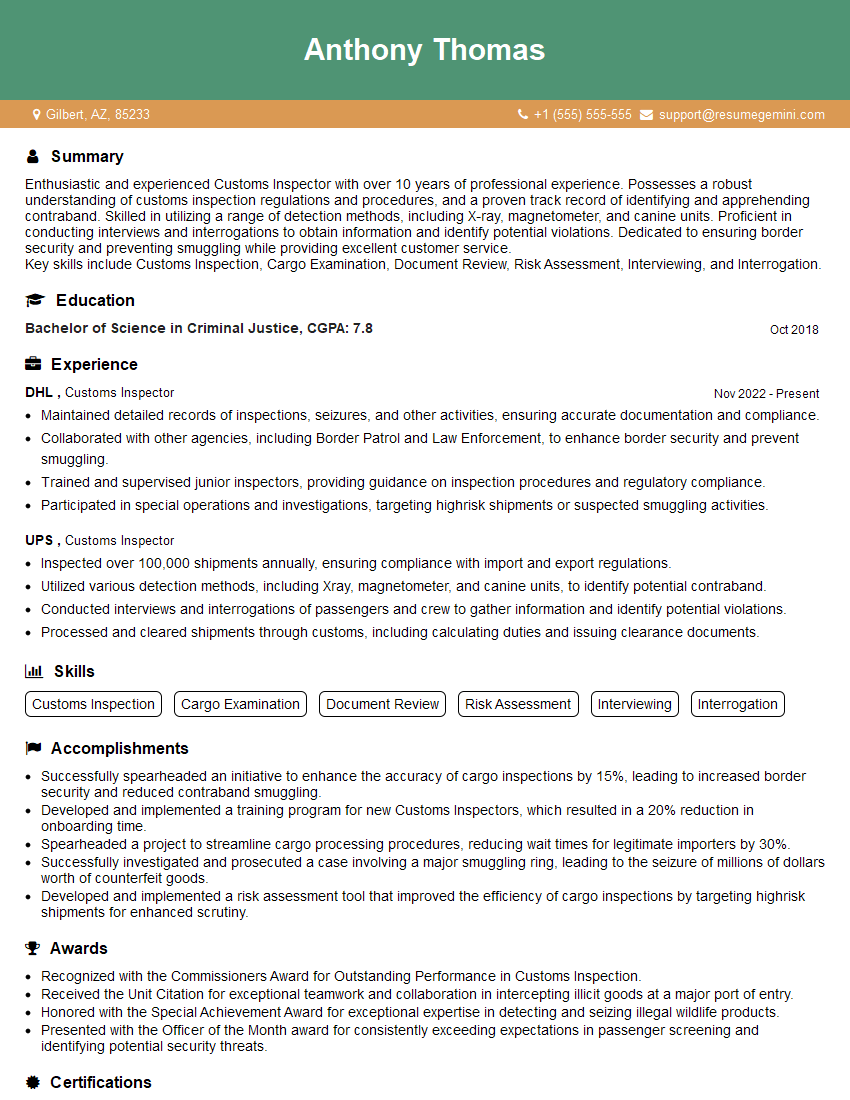
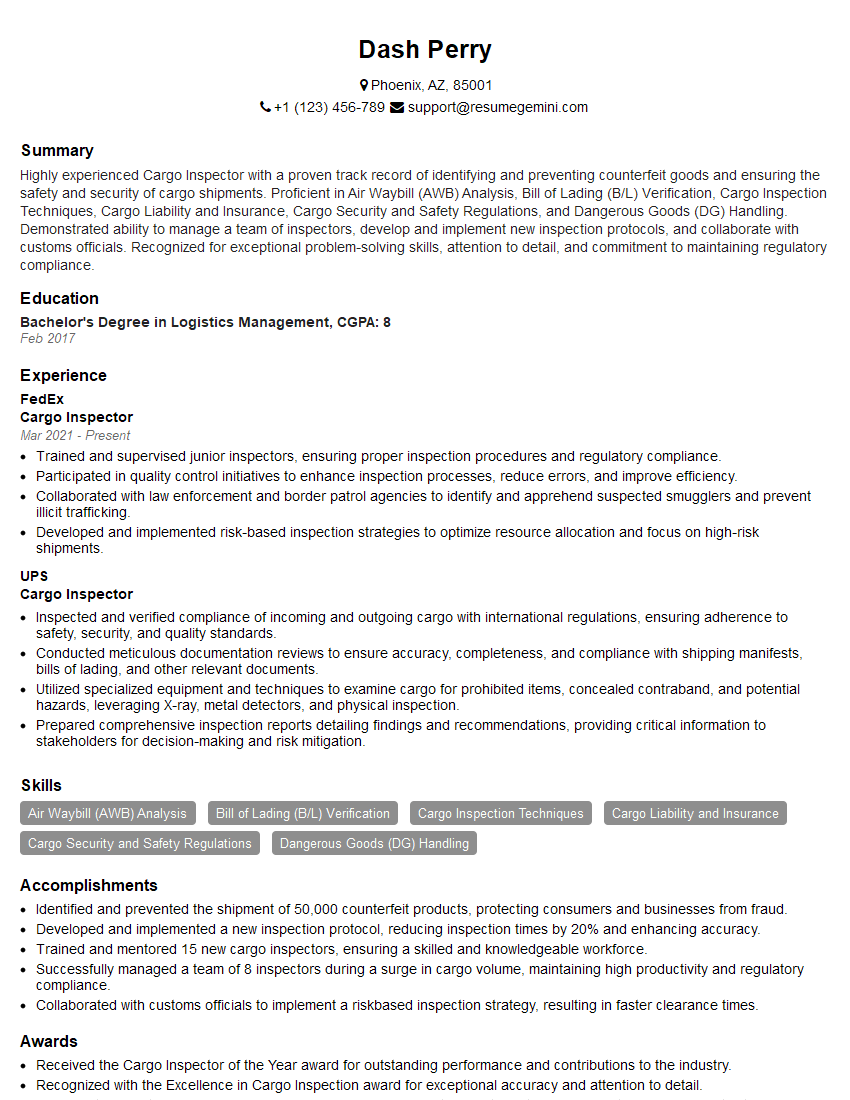
Mastering Cargo Inspection and Security opens doors to a rewarding career with excellent growth potential in a vital industry. To maximize your job prospects, creating an ATS-friendly resume is essential. ResumeGemini is a trusted resource to help you build a professional and impactful resume that showcases your skills and experience effectively. ResumeGemini provides examples of resumes tailored specifically to the Cargo Inspection and Security field, helping you present yourself as the ideal candidate. Take the next step towards your dream career today!
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Amazing blog
hello,
Our consultant firm based in the USA and our client are interested in your products.
Could you provide your company brochure and respond from your official email id (if different from the current in use), so i can send you the client’s requirement.
Payment before production.
I await your answer.
Regards,
MrSmith
hello,
Our consultant firm based in the USA and our client are interested in your products.
Could you provide your company brochure and respond from your official email id (if different from the current in use), so i can send you the client’s requirement.
Payment before production.
I await your answer.
Regards,
MrSmith
These apartments are so amazing, posting them online would break the algorithm.
https://bit.ly/Lovely2BedsApartmentHudsonYards
Reach out at BENSON@LONDONFOSTER.COM and let’s get started!
Take a look at this stunning 2-bedroom apartment perfectly situated NYC’s coveted Hudson Yards!
https://bit.ly/Lovely2BedsApartmentHudsonYards
Live Rent Free!
https://bit.ly/LiveRentFREE
Interesting Article, I liked the depth of knowledge you’ve shared.
Helpful, thanks for sharing.
Hi, I represent a social media marketing agency and liked your blog
Hi, I represent an SEO company that specialises in getting you AI citations and higher rankings on Google. I’d like to offer you a 100% free SEO audit for your website. Would you be interested?