Interviews are opportunities to demonstrate your expertise, and this guide is here to help you shine. Explore the essential Close Protection and Dignitary Security interview questions that employers frequently ask, paired with strategies for crafting responses that set you apart from the competition.
Questions Asked in Close Protection and Dignitary Security Interview
Q 1. Describe your experience in risk assessment and mitigation strategies for high-profile individuals.
Risk assessment for high-profile individuals is a meticulous process involving identifying, analyzing, and prioritizing potential threats. It’s not just about physical security; it encompasses reputational, financial, and even cyber risks. My approach begins with a thorough background check of the principal, analyzing their public profile, known associates, and potential adversaries. This informs the development of a comprehensive threat matrix, categorizing risks by likelihood and impact.
Mitigation strategies are tailored to the specific threats identified. This might involve implementing robust physical security measures like advanced surveillance systems, secure transportation protocols, and a dedicated close protection team. It could also involve developing communication strategies to manage public perception, implementing cybersecurity protocols to protect against online threats, or even working with law enforcement agencies to proactively address specific concerns. For example, if a client receives credible death threats, we’d immediately increase their security detail, potentially utilizing armored vehicles and adjusting travel routes to minimize exposure. We would also collaborate with law enforcement to investigate the source of the threat.
Q 2. Explain your understanding of different threat levels and how they influence security protocols.
Threat levels are typically categorized using a standardized system, often ranging from low to extreme. This classification influences every aspect of security planning. A low-level threat might involve minimal security presence and reliance on proactive measures like background checks. Conversely, an extreme threat necessitates a heavily fortified security perimeter, 24/7 surveillance, robust counter-surveillance measures, and a significant close protection team.
For example, a routine public appearance might warrant a low to moderate threat level, requiring a small, discreet security detail and basic situational awareness. However, an appearance at a high-risk event, such as a large political rally in a volatile region, would necessitate a comprehensive security plan involving advanced threat assessment, intelligence gathering, and a substantial security presence, potentially incorporating specialized equipment and personnel.
Q 3. What are your methods for conducting surveillance and identifying potential threats?
Surveillance and threat identification employ a multi-faceted approach. This includes both overt and covert surveillance methods. Overt surveillance might involve visible security personnel, CCTV cameras, and access control systems. Covert methods are more discreet and may involve utilizing specialized observation techniques, electronic surveillance equipment (with appropriate legal authority), and open-source intelligence gathering to monitor potential threats.
Identifying threats involves analyzing patterns of behavior, identifying individuals who exhibit suspicious behavior, tracking vehicles that might be following the principal, and using technical intelligence to detect potential threats. For example, we might use social media monitoring to identify individuals expressing violent intentions towards the client or we might conduct physical surveillance around the client’s residence to look for suspicious activity.
Q 4. How would you handle a hostile confrontation or an attempted abduction?
Handling hostile confrontations and abduction attempts is about prioritizing the principal’s safety and de-escalation. This is where extensive training in defensive tactics and emergency response protocols is crucial. In a confrontation, our primary goal is to create distance, secure the principal, and ensure their safety while contacting law enforcement. This might involve employing evasive maneuvers, employing defensive tactics to protect the principal (only when absolutely necessary), and using communication skills to de-escalate a situation.
An abduction attempt would necessitate immediate and decisive action. This might involve employing counter-abduction techniques like creating diversions, using vehicles to block escape routes, and utilizing tactical maneuvers to disrupt the attackers. Simultaneously, we would maintain constant communication with law enforcement and relay critical information for a coordinated response.
Q 5. Detail your experience with advanced driving techniques and defensive driving maneuvers.
Advanced driving techniques and defensive driving are essential components of close protection. This involves proficiency in evasive driving maneuvers, vehicle control in emergency situations, and understanding of tactical driving techniques. My training includes high-speed driving, counter-ambush procedures, and safe driving in challenging environments.
For example, I’m trained to perform emergency braking techniques, j-turns, and other maneuvers to quickly evade threats while keeping the principal safe. Understanding the vehicle’s capabilities and limitations is crucial. Knowing how to react to a sudden tire blow-out, navigate through challenging road conditions, or handle a vehicle malfunction are all key aspects of defensive driving in a close protection context.
Q 6. Describe your knowledge of counter-surveillance techniques.
Counter-surveillance involves detecting and evading surveillance attempts. This requires a high level of awareness and understanding of surveillance techniques. It involves regularly scanning surroundings, recognizing typical surveillance patterns (vehicles, individuals, electronic devices), and employing countermeasures to disrupt or evade surveillance.
Techniques include using different routes to avoid predictable patterns, varying speeds and driving styles, using decoys, and implementing electronic countermeasures (where legally permissible). For example, we might change a client’s daily routines or use countermeasures to detect and disrupt attempts to track the client’s electronic devices.
Q 7. How do you maintain situational awareness in dynamic environments?
Maintaining situational awareness in dynamic environments is paramount. It’s a constant process involving observation, analysis, and anticipation. This includes assessing the environment, identifying potential threats, and anticipating their actions. This involves utilizing all senses, paying attention to subtle cues, and continuously scanning the surrounding environment for any changes or anomalies.
For example, in a crowded marketplace, I would be constantly scanning the crowd for anyone who might be following us, paying attention to unusual behavior, and having a pre-planned escape route in mind. Regularly communicating with team members ensures a shared understanding of the situation and allows for a coordinated response if a threat is detected.
Q 8. What communication protocols do you utilize in a close protection team?
Effective communication is the cornerstone of any successful close protection team. We utilize a multi-layered approach, combining clear, concise verbal communication with discreet, pre-arranged hand signals and potentially encrypted communication devices.
- Verbal Communication: Clear, concise briefings before any operation are crucial, establishing roles, responsibilities, and potential threats. During operations, communication is kept brief and to the point to avoid drawing unwanted attention. For example, ‘Principal is compromised’ would immediately alert the team to a serious situation requiring immediate action.
- Hand Signals: A standardized system of hand signals allows for silent communication in situations where verbal communication is undesirable or impossible. These signals cover everything from potential threats to changes in the principal’s itinerary or a medical emergency. For example, a specific hand signal might indicate the need for immediate evacuation or the presence of a suspicious individual.
- Encrypted Communication: In high-risk environments, encrypted communication devices are essential to maintaining confidentiality and security. This protects sensitive information from interception.
Regular communication drills ensure the team functions as a cohesive unit, reacting swiftly and efficiently to various scenarios.
Q 9. Explain your understanding of international security protocols and regulations.
My understanding of international security protocols and regulations is extensive, encompassing factors like local laws, threat assessments, and international treaties. This includes familiarity with the Vienna Convention on Diplomatic Relations, which governs the protection of diplomatic personnel.
Understanding specific country regulations is paramount, as legal frameworks and security protocols vary significantly across regions. For example, firearm laws and the use of force regulations differ greatly between the US and European countries. Therefore, thorough pre-operation planning and research are critical for any international assignment. Furthermore, I’m knowledgeable about various threat assessments from international organizations like Interpol, allowing us to anticipate potential risks and adapt accordingly.
Successful international operations require cultural sensitivity and awareness of potential local sensitivities. For instance, understanding local customs and protocols avoids unintentional breaches of etiquette which could jeopardize security.
Q 10. How would you react to a medical emergency involving the principal?
In a medical emergency involving the principal, immediate action is paramount. My response would be based on a tiered approach:
- Assessment: First, I’d assess the nature and severity of the medical emergency. This involves quickly determining the type of injury or illness, the principal’s condition (consciousness, breathing, etc.), and the immediate environment.
- Emergency Response: I’d immediately alert the rest of the close protection team and any pre-arranged medical personnel. If the situation is life-threatening, I’d begin administering first aid to the best of my abilities while maintaining security of the principal.
- Medical Evacuation: This would involve coordinating with emergency services, securing a safe route to the nearest appropriate medical facility, and ensuring the principal’s safety during transportation. This might involve using a designated vehicle, a pre-arranged emergency helicopter, or similar.
- Post-Incident Procedures: Following the incident, I’d fully cooperate with any investigation and complete a detailed after-action report to identify areas for improvement in our procedures.
This entire process is drilled regularly to ensure a fast and efficient response. The key is to prioritize the principal’s safety and well-being while maintaining security and control.
Q 11. Describe your experience with close protection planning and route selection.
Close protection planning and route selection are crucial to mission success. My experience includes extensive work in pre-assignment site surveys, threat assessments, and route planning software.
The process begins with a thorough risk assessment. This examines potential threats, including known hostile actors, public events, and infrastructure vulnerabilities. We then identify multiple potential routes, analyzing each for potential risks and advantages. This might involve studying traffic patterns, identifying safe havens, and anticipating potential points of congestion or vulnerability.
Route selection often involves utilizing satellite imagery, local maps, and even real-time traffic data. We simulate the route to assess response times in case of an incident. For instance, we’ll check the proximity of emergency services and escape routes. Finally, we brief the team thoroughly on the planned route, contingency plans, and communication protocols.
In practice, we’ve worked on high-profile events where meticulous route planning was critical to successful principal movement. For example, during a recent presidential visit, we planned and executed several alternate routes to mitigate traffic congestion and potential protest activity.
Q 12. What is your familiarity with different types of weaponry and their effective countermeasures?
My familiarity with weaponry extends to both offensive and defensive weapons, as well as countermeasures. This isn’t about personal use of offensive weaponry, but about recognizing, assessing, and mitigating threats.
I’m trained to recognize various firearm types, improvised explosive devices (IEDs), and other potential weapons. Understanding their capabilities is crucial to countermeasure development. This might involve identifying potential ambush points based on the range of different weapons.
Countermeasures include advanced defensive driving techniques, evasive maneuvers, and the strategic use of cover and concealment. We also utilize electronic countermeasures, depending on the threat level. We might use jammers to disrupt hostile communications, or specialized protective equipment. Training is extensive and continually updated to keep pace with the evolving nature of threats. Furthermore, the team undergoes regular firearms familiarization to identify and react to the presence of weapons, but only as part of a defensive strategy.
Q 13. How do you manage stress and maintain composure under pressure?
Stress management and composure under pressure are essential for close protection officers. We employ several techniques to maintain effectiveness in high-stress situations.
- Physical Fitness: Maintaining peak physical fitness enhances stress tolerance. Regular exercise and a healthy lifestyle build resilience.
- Mental Training: Techniques like mindfulness and meditation help manage anxiety and maintain focus. Regular scenario-based training prepares us mentally and physically for stressful situations.
- Teamwork and Support: Strong teamwork fosters mutual support and reduces individual burden during crises. Open communication and trust are key.
- Professional Detachment: While empathy is vital for client well-being, maintaining a level of professional detachment prevents emotional overwhelm during emergencies.
These strategies are not merely theoretical. They are practiced regularly through drills, physical training, and psychological debriefings. The goal is to cultivate a calm and effective response in even the most demanding circumstances.
Q 14. How would you handle a media scrum or paparazzi situation?
Handling media scrums and paparazzi situations requires a balanced approach, prioritizing the principal’s safety and well-being while maintaining a professional demeanor.
Our strategy involves a combination of preventative measures and reactive responses. Preventative measures might include pre-arranged routes to avoid high-traffic areas and coordinating with local authorities to manage crowds.
When confronted with a scrum, our priority is to create a physical barrier between the principal and the media, ensuring a safe and controlled movement. This may involve utilizing vehicles, security personnel, and even physical maneuvering techniques. We avoid confrontation but will firmly, yet politely, direct the press away from the principal. If needed, we’ll coordinate with law enforcement to maintain order.
Throughout, maintaining a professional and controlled demeanor is crucial to avoid escalating the situation. Our aim is to de-escalate while ensuring the safety of the principal, avoiding aggressive interactions or actions that might provoke the situation further.
Q 15. Describe your experience with personal security equipment (PSE) and its maintenance.
Personal Security Equipment (PSE) is crucial for close protection. My experience encompasses a wide range of equipment, from basic items like handcuffs and restraints to more advanced technology like covert surveillance devices and communication systems. Proper maintenance is paramount for effectiveness and safety. This involves regular inspections for damage or wear, ensuring functionality through testing and calibration, and adhering to strict cleaning and storage protocols. For example, I regularly check the battery life and functionality of radios, ensuring they are always charged and ready for use. I also ensure that all restraints are in good working order and stored securely, preventing accidental deployment or damage. Maintaining detailed records of inspections and maintenance is essential for traceability and accountability.
- Example: Before each assignment, I conduct a thorough check of my body armor, ensuring it fits correctly and that all components are functional. This includes checking the ballistic plates for any signs of damage and the vest itself for wear and tear.
- Example: Regular cleaning and lubrication of firearms (where legally permitted and required) are essential for reliable performance. This includes thorough cleaning after every use and periodic lubrication to prevent corrosion and ensure smooth operation.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. How would you conduct a pre-assignment security survey of a location?
A pre-assignment security survey is a critical step. It’s a methodical process of assessing potential threats and vulnerabilities at a location before a principal’s arrival. I would begin by carefully studying maps and blueprints of the location, identifying potential entry and exit points, blind spots, and escape routes. Then, I’d conduct a physical reconnaissance, paying close attention to security measures already in place (e.g., CCTV cameras, access control systems, security personnel), identifying weaknesses, and assessing the surrounding environment for potential threats (e.g., crowds, construction, potential ambush points). I would also consider the specific needs of the principal, their travel routes, and the duration of their stay. The final step involves preparing a detailed report outlining the identified risks and recommending appropriate security measures. For example, I might identify a lack of adequate lighting in a parking area as a potential vulnerability, recommending the use of additional lighting or security personnel in that area.
- Step-by-step process:
- Desk Research
- Physical Reconnaissance
- Risk Assessment
- Report Preparation
Q 17. Explain your understanding of security technology and its integration into close protection operations.
Security technology plays a vital role. My understanding encompasses a broad spectrum of technologies, from basic surveillance systems to advanced biometric access control and threat detection systems. Integration into close protection operations requires careful planning and coordination. For instance, I utilize GPS tracking devices to monitor the principal’s location and movements, enhancing situational awareness. Discreet communication systems are also crucial for maintaining contact with the team and emergency services. I’m proficient in using and assessing technologies such as CCTV footage review, threat analysis software, and encrypted communication channels. The key is to leverage technology to enhance security without compromising the principal’s privacy or safety, while ensuring the technology’s reliability and the team’s proficiency in its usage.
- Example: Using encrypted communication systems to relay information between team members, ensuring confidentiality and preventing interception by unauthorized parties.
- Example: Integrating GPS tracking data with real-time threat analysis software to proactively identify and mitigate potential risks.
Q 18. How would you handle a breach of security?
Handling a security breach requires immediate, decisive action. The first step is to assess the situation—determine the nature of the breach, the level of threat, and the immediate danger to the principal. Next, I would implement pre-planned emergency procedures, prioritizing the safety and evacuation of the principal. This might involve using tactical maneuvers, creating diversions, or utilizing the available security technology and personnel to neutralize or contain the threat. Post-incident, a thorough debriefing would take place, focusing on identifying the shortcomings in the security plan and implementing corrective measures to prevent future breaches. Reporting to relevant authorities is also a critical step in ensuring accountability and aiding in investigations.
- Example: If confronted with an aggressive individual, using distraction and evasion techniques to create an opportunity for the principal’s safe removal from the immediate vicinity, while simultaneously alerting other team members and requesting assistance.
- Example: In the event of a vehicle pursuit, utilizing advanced driving techniques to safely maneuver the vehicle while maintaining communication with other team members and law enforcement.
Q 19. Describe your experience with working in diverse cultural settings.
Working in diverse cultural settings is essential in this field. I have extensive experience operating in various countries and cultures, requiring adaptation to different customs, laws, and social norms. This involves understanding and respecting local traditions, communicating effectively despite language barriers, and building rapport with local law enforcement and security personnel. Cultural sensitivity is crucial; for instance, understanding acceptable levels of physical contact and personal space varies widely across cultures. Successful operation requires careful planning and research, as well as a willingness to learn and adapt to new environments.
- Example: While working in a Middle Eastern country, I took the time to understand the local customs regarding greetings and interactions with women, adjusting my behavior accordingly to show respect and avoid causing offense.
- Example: Working in a country with limited English proficiency, I utilized translators and visual aids to effectively communicate security instructions and procedures.
Q 20. How would you maintain confidentiality and discretion while performing your duties?
Maintaining confidentiality and discretion is paramount. This involves adhering to strict non-disclosure agreements, protecting sensitive information, and avoiding any actions that could compromise the principal’s privacy or security. This includes using secure communication channels, carefully managing information sharing, and exercising discretion in all interactions. I understand the importance of not discussing operational details with unauthorized individuals and of maintaining a professional demeanor at all times, even in challenging situations. Building trust and maintaining professional boundaries are key elements. Even seemingly innocuous information could compromise the principal’s security if it falls into the wrong hands.
Q 21. Explain your understanding of legal liabilities associated with close protection work.
Legal liabilities in close protection are significant. This includes understanding the laws pertaining to use of force, weapons possession, and liability for negligence or harm caused to the principal or third parties. I’m well-versed in relevant laws in various jurisdictions and ensure all actions are within the confines of the law. Staying updated on legal changes and best practices is vital. Professional indemnity insurance is also a crucial aspect, offering protection against potential legal claims arising from the performance of duties. Maintaining meticulous records of all actions and incidents is also critical for legal defense, should the need arise. A thorough understanding of legal frameworks and best practices is necessary for responsible and legally compliant operations.
Q 22. What is your experience with physical fitness and self-defense techniques?
Maintaining peak physical fitness is paramount in close protection. My regimen includes regular strength training, cardiovascular exercise, and flexibility work to ensure I can react effectively and protect the principal under duress. This goes beyond simply being strong; it’s about endurance, agility, and quick reflexes. Self-defense techniques are a crucial component. I’m proficient in various martial arts, including Krav Maga and hand-to-hand combat, focused on practical, defensive applications rather than offensive maneuvers. My training emphasizes de-escalation and neutralizing threats without unnecessary violence, prioritizing the safety of both the principal and myself. I regularly undergo advanced training to refine my skills and adapt to evolving threats. For instance, recent training included specialized techniques for close-quarters combat in confined spaces and crowd control strategies.
Q 23. How would you manage a compromised communication system?
A compromised communication system is a critical security vulnerability. My immediate response would involve a layered approach. First, I’d attempt to troubleshoot the existing system—checking for signal strength, power sources, and potential interference. Simultaneously, I’d activate backup communication methods. This could include pre-arranged alternative communication channels such as satellite phones, pre-paid burner phones, or secure messaging applications with end-to-end encryption. I would also utilize visual communication methods, such as pre-arranged hand signals with other security personnel, to relay critical information. Depending on the nature of the compromise, I might need to establish secure communication channels with law enforcement or other relevant agencies, prioritizing the safety of the principal. Regular testing and redundancy are key; we conduct frequent drills simulating communication failures to ensure team preparedness.
Q 24. Describe your experience with crisis management and emergency response protocols.
My experience in crisis management and emergency response protocols is extensive. I’ve participated in numerous high-stakes scenarios, including active shooter drills, hostage situations simulations, and emergency evacuations. My training encompasses a range of threats, from natural disasters to targeted attacks. I’m proficient in risk assessment, threat analysis, and developing comprehensive emergency plans tailored to specific situations. The key is to remain calm under pressure, execute pre-planned procedures efficiently, and adapt to unforeseen circumstances. For example, during a recent security detail for a high-profile CEO, a bomb threat necessitated an immediate evacuation. By utilizing my knowledge of evacuation procedures, coordinating with local law enforcement, and executing our pre-determined contingency plan, we ensured the CEO’s safety with minimal disruption.
Q 25. How do you adapt your security plan to unexpected events or changing circumstances?
Adaptability is crucial in close protection. Unexpected events are inevitable; therefore, flexibility is built into every security plan. My approach involves constant situational awareness, anticipating potential problems, and having contingency plans in place. For example, if a planned route becomes unsafe due to a sudden protest, I’d immediately reroute, selecting a safer alternative while ensuring the principal’s continued safety and minimizing any disruption to their schedule. This requires clear communication with the principal, the security team, and relevant stakeholders. Continuous monitoring of real-time intelligence, such as news reports and social media, is also vital for anticipating and responding to evolving threats or circumstances. Regular review and modification of the security plan based on past experiences and lessons learned are also critical for ongoing improvement.
Q 26. What is your experience with working with law enforcement and other security agencies?
Effective collaboration with law enforcement and other security agencies is vital. Over the years, I’ve cultivated strong working relationships with various agencies, building trust and facilitating seamless coordination during emergencies. This includes providing preemptive briefings to relevant authorities about the security plan, ensuring clear communication channels are established, and sharing intelligence proactively. During an incident, this collaborative approach enables rapid response and efficient resource allocation. For example, during a recent event, coordinating with local police allowed for a swift and discreet response to a potential threat, minimizing disruption to the principal’s activities and preventing any escalation.
Q 27. Describe a situation where you had to make a quick decision under pressure. What was the outcome?
During a VIP motorcade, a sudden and unexpected road blockage occurred due to a serious accident ahead. I had to make a split-second decision to reroute the motorcade through a less traveled but equally secure alternative route. This involved instantly assessing the risk, communicating the change to the driver and other security personnel, and ensuring the principal’s safety while maintaining the integrity of the security perimeter. The success of this decision lay in proactive planning, thorough route familiarization, and the seamless execution of the contingency plan. The outcome was a successful rerouting of the motorcade, ensuring the principal arrived safely and on time, despite the unexpected obstruction.
Q 28. How do you ensure the safety and wellbeing of the principal while maintaining their privacy and freedom of movement?
Balancing the principal’s safety, privacy, and freedom of movement requires a delicate yet firm approach. It’s about creating an invisible shield of protection rather than a restrictive cage. This involves discreet observation, proactive risk mitigation, and adapting security measures to different contexts. For instance, we might use less visible security details in less high-risk environments, while maintaining constant vigilance. In public appearances, we might coordinate with event organizers to manage crowds and control access points, while ensuring the principal’s movements remain relatively fluid and natural. This requires understanding the principal’s preferences and working collaboratively with them to build trust and ensure their comfort while remaining proactive in threat identification and mitigation. Regular review and adjustments to the security posture are key to ensuring this balance is maintained.
Key Topics to Learn for Close Protection and Dignitary Security Interview
- Risk Assessment and Management: Understanding and mitigating potential threats to the principal. Practical application includes developing pre-assignment security plans and real-time threat analysis.
- Advanced Driving Techniques: Evacuation procedures, defensive driving maneuvers, and route planning for secure transportation. Consider the nuances of driving in various terrains and under pressure.
- Close Protection Tactics and Techniques: Personal protection techniques, formations, and communication protocols. Think about adapting techniques based on the environment and the principal’s specific needs.
- Surveillance Detection and Countermeasures: Identifying and responding to surveillance attempts. Explore various methods of surveillance and the strategies used to counter them.
- Security Planning and Coordination: Developing and implementing security plans for events, travel, and static locations. Consider the collaborative aspects of working with other security personnel and agencies.
- Legal and Ethical Considerations: Understanding the legal framework governing close protection work, and maintaining ethical standards. This includes awareness of use-of-force guidelines and potential legal ramifications.
- Communication and Teamwork: Effective communication within the protection team and with other stakeholders. Practical application involves clear, concise, and proactive reporting.
- First Aid and Emergency Response: Providing immediate medical assistance and handling emergency situations. This extends to understanding various emergency procedures and relevant protocols.
- Physical Fitness and Self-Defense: Maintaining a high level of physical fitness and proficiency in self-defense techniques. Focus on stamina, strength, and situational awareness.
- Principal’s Needs and Preferences: Understanding and adapting to the specific needs and preferences of the principal. This includes anticipating their requirements and adjusting security protocols accordingly.
Next Steps
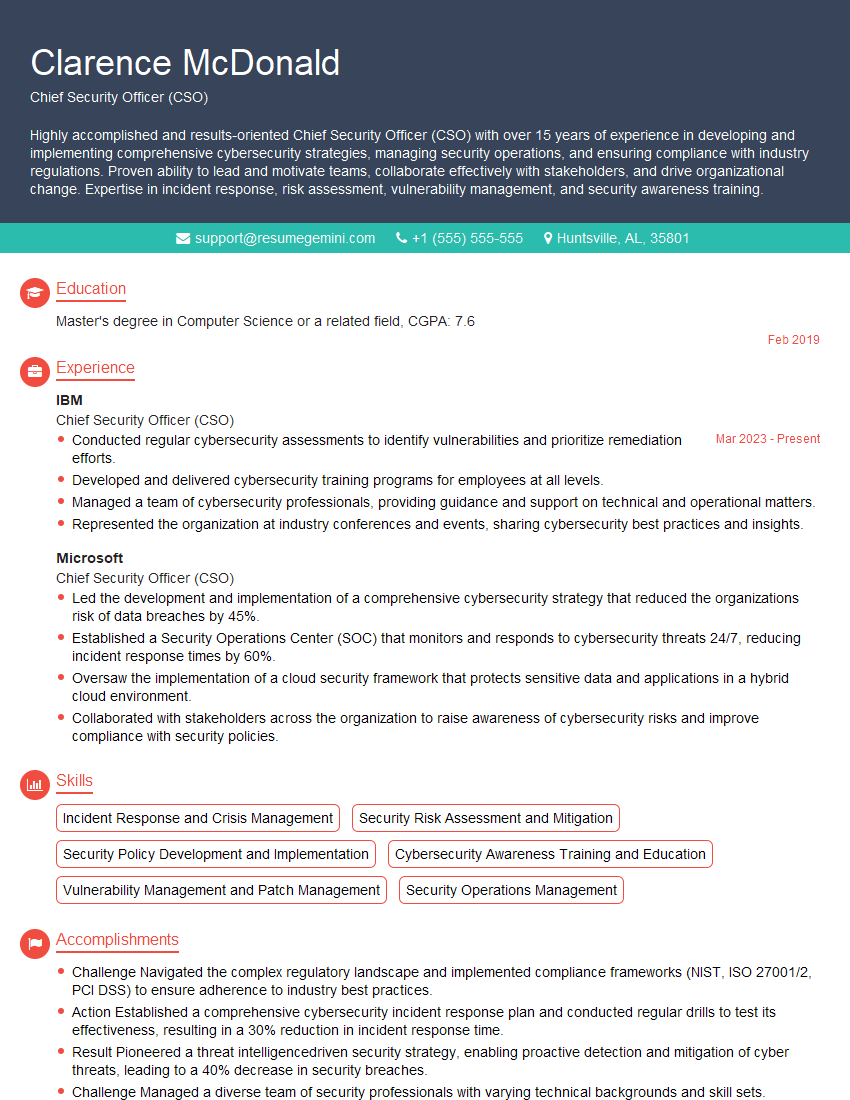
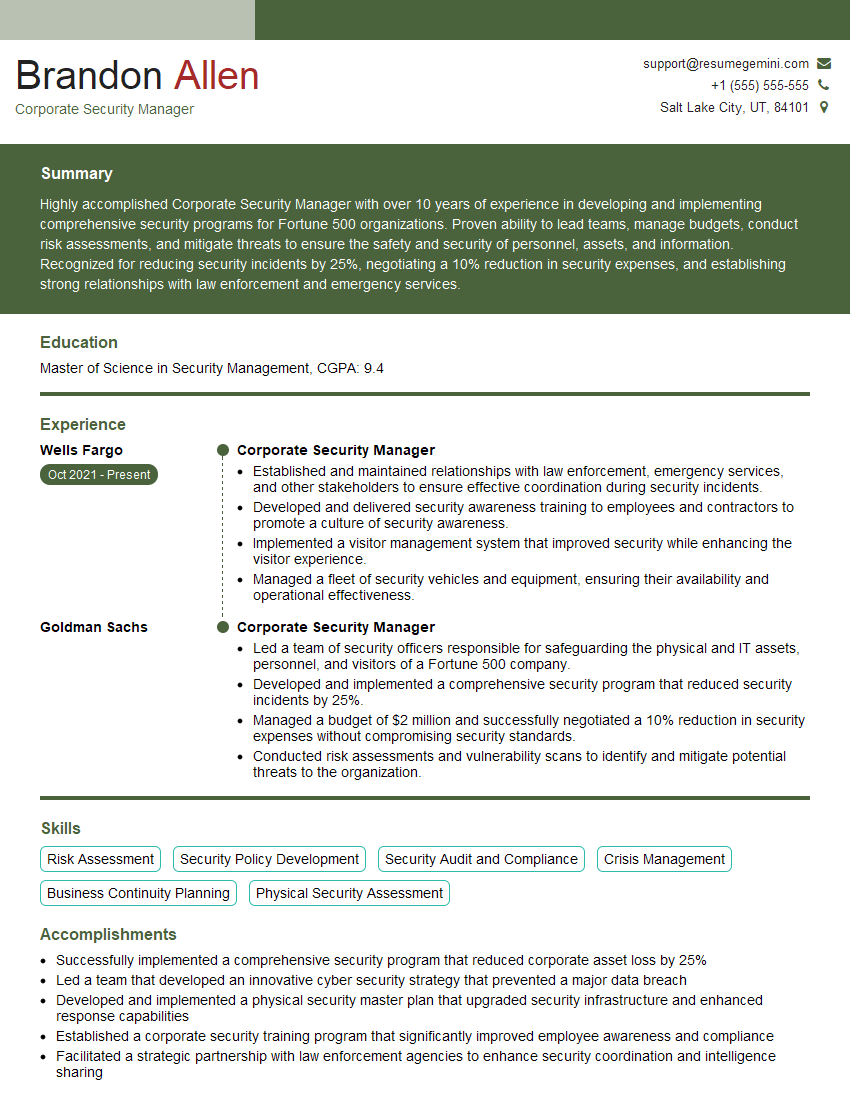
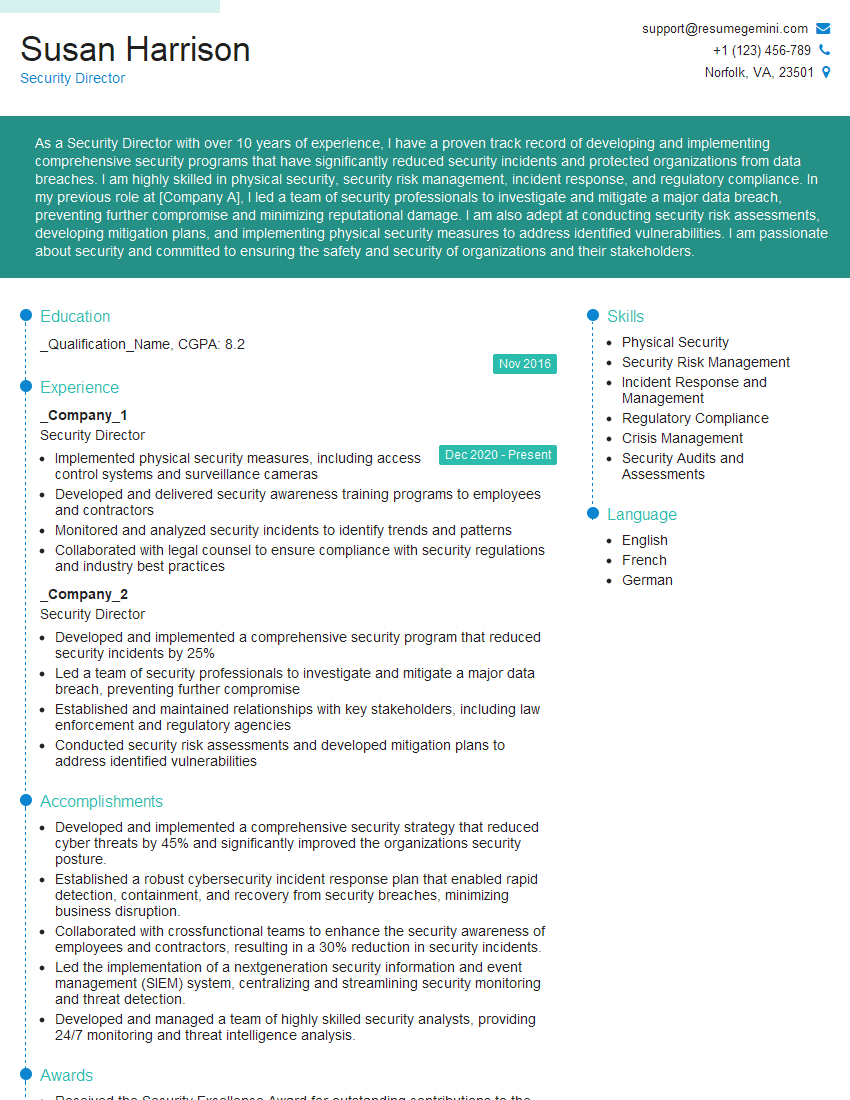
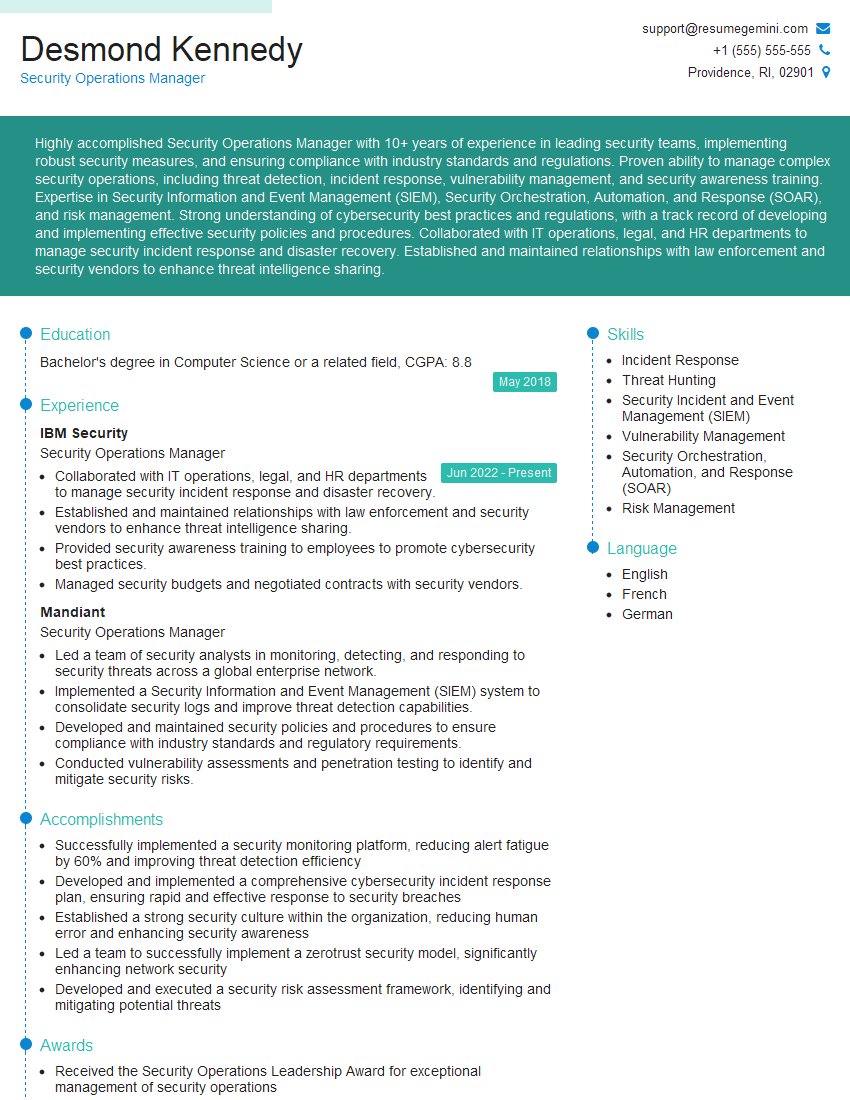
Mastering Close Protection and Dignitary Security opens doors to a rewarding and impactful career, offering excellent growth potential and the opportunity to make a real difference. To maximize your job prospects, creating a strong, ATS-friendly resume is crucial. ResumeGemini is a trusted resource that can help you build a professional and effective resume tailored to highlight your unique skills and experience. Examples of resumes specifically designed for Close Protection and Dignitary Security roles are available to help you craft the perfect application.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Amazing blog
hello,
Our consultant firm based in the USA and our client are interested in your products.
Could you provide your company brochure and respond from your official email id (if different from the current in use), so i can send you the client’s requirement.
Payment before production.
I await your answer.
Regards,
MrSmith
hello,
Our consultant firm based in the USA and our client are interested in your products.
Could you provide your company brochure and respond from your official email id (if different from the current in use), so i can send you the client’s requirement.
Payment before production.
I await your answer.
Regards,
MrSmith
These apartments are so amazing, posting them online would break the algorithm.
https://bit.ly/Lovely2BedsApartmentHudsonYards
Reach out at BENSON@LONDONFOSTER.COM and let’s get started!
Take a look at this stunning 2-bedroom apartment perfectly situated NYC’s coveted Hudson Yards!
https://bit.ly/Lovely2BedsApartmentHudsonYards
Live Rent Free!
https://bit.ly/LiveRentFREE
Interesting Article, I liked the depth of knowledge you’ve shared.
Helpful, thanks for sharing.
Hi, I represent a social media marketing agency and liked your blog
Hi, I represent an SEO company that specialises in getting you AI citations and higher rankings on Google. I’d like to offer you a 100% free SEO audit for your website. Would you be interested?