Cracking a skill-specific interview, like one for SWE, requires understanding the nuances of the role. In this blog, we present the questions you’re most likely to encounter, along with insights into how to answer them effectively. Let’s ensure you’re ready to make a strong impression.
Questions Asked in SWE Interview
Q 1. Explain the difference between a process and a thread.
Imagine a restaurant. The process is like the entire operation – from taking orders to cooking to serving. A thread, on the other hand, is a single waiter attending to multiple tables simultaneously within that operation.
In software, a process is an independent, self-contained execution environment. It has its own memory space, system resources, and security context. Starting a new process is resource-intensive. Think of launching a completely separate program on your computer.
A thread, conversely, is a lightweight unit of execution within a process. Multiple threads share the same memory space and resources of their parent process. Creating a new thread is less resource-intensive than creating a process. Think of multiple waiters (threads) working within the same restaurant (process).
Key Differences Summarized:
- Memory Space: Processes have separate memory spaces; threads share a common memory space.
- Resource Usage: Processes consume more resources than threads.
- Communication: Inter-process communication (IPC) is more complex than inter-thread communication.
- Creation Overhead: Creating a process is more expensive than creating a thread.
Example: A web server might use multiple processes to handle multiple client requests concurrently, and each process could employ multiple threads to manage different aspects of a single request (e.g., one thread for handling database interaction, another for generating the response).
Q 2. What are the SOLID principles of object-oriented design?
The SOLID principles are five design principles intended to make software designs more understandable, flexible, and maintainable. They are particularly relevant in object-oriented programming.
- Single Responsibility Principle (SRP): A class should have only one reason to change. This prevents classes from becoming bloated and difficult to manage. For example, a
Userclass should only handle user-related logic, not database interactions. - Open/Closed Principle (OCP): Software entities (classes, modules, functions, etc.) should be open for extension, but closed for modification. This principle promotes extensibility without breaking existing code. Think of using interfaces or abstract classes to add new functionality.
- Liskov Substitution Principle (LSP): Subtypes should be substitutable for their base types without altering the correctness of the program. If a function works with a base class, it should also work with any of its subclasses without any issues.
- Interface Segregation Principle (ISP): Clients should not be forced to depend upon interfaces they don’t use. Instead of one large interface, it’s better to have several smaller, more specific interfaces. This prevents classes from implementing methods they don’t need.
- Dependency Inversion Principle (DIP): High-level modules should not depend on low-level modules. Both should depend on abstractions. Abstractions should not depend on details. Details should depend on abstractions. This promotes loose coupling and makes code more flexible and testable. This often involves using interfaces and dependency injection.
Following SOLID principles leads to more robust, maintainable, and testable code, saving time and resources in the long run.
Q 3. Describe your experience with Agile methodologies.
I have extensive experience working within Agile methodologies, primarily Scrum and Kanban. In my previous role at [Previous Company Name], we utilized Scrum for most projects. This involved daily stand-ups, sprint planning, sprint reviews, and retrospectives. I was responsible for [Specific tasks, e.g., story estimation, task completion, participation in sprint planning].
We also employed Kanban for smaller, ongoing projects where a fixed sprint cycle wasn’t ideal. This allowed for greater flexibility and responsiveness to changing priorities. I found the iterative nature of Agile to be highly effective in delivering high-quality software incrementally, enabling continuous feedback and adaptation throughout the development process.
My experience includes working with tools like Jira and Confluence for project management and collaboration. I am comfortable with various Agile ceremonies and understand the importance of continuous improvement and adapting practices to suit the specific project needs.
Q 4. Explain the concept of RESTful APIs.
RESTful APIs (Representational State Transfer Application Programming Interfaces) are a set of architectural constraints for building web services. They emphasize a stateless, client-server architecture where the client and server interact through standard HTTP methods (GET, POST, PUT, DELETE) to manipulate resources.
Key Characteristics:
- Stateless: Each request from the client contains all the information necessary for the server to process it. The server doesn’t need to store any context between requests.
- Client-Server: A clear separation between the client and the server.
- Cacheable: Responses can be cached to improve performance.
- Uniform Interface: A consistent way of interacting with resources using standard HTTP methods and data formats (like JSON or XML).
- Layered System: Clients don’t need to know the internal architecture of the server.
- Code on Demand (Optional): The server can optionally provide executable code to the client (e.g., JavaScript).
Example: A typical REST API endpoint might look like this: /users/123. A GET request to this endpoint would retrieve information about user with ID 123. A PUT request could update the user’s information, and a DELETE request would delete the user.
Q 5. What are the advantages and disadvantages of using microservices?
Microservices architecture involves breaking down a large application into smaller, independent services. Each service focuses on a specific business function and can be developed, deployed, and scaled independently.
Advantages:
- Improved Scalability: Individual services can be scaled independently based on their specific needs.
- Increased Agility and Faster Deployment: Smaller services are easier to develop, test, and deploy.
- Enhanced Fault Isolation: A failure in one service doesn’t necessarily bring down the entire application.
- Technology Diversity: Different services can be built using different technologies best suited for their tasks.
- Easier Maintenance and Updates: Smaller codebases are easier to understand and maintain.
Disadvantages:
- Increased Complexity: Managing a large number of services can be complex.
- Distributed System Challenges: Dealing with issues like network latency and data consistency across multiple services.
- Operational Overhead: More services mean more infrastructure and monitoring.
- Testing and Debugging Challenges: Testing interactions between services can be more complex.
The decision to use microservices depends on the specific needs of the project. It’s not always the best approach, especially for smaller applications.
Q 6. How do you handle concurrency in your code?
Handling concurrency depends heavily on the specific programming language and the nature of the task. However, some common strategies include:
- Threads and Thread Pools: Using multiple threads to execute tasks concurrently, often managed by a thread pool to control resource usage. This is common in Java and other multithreaded languages.
- Asynchronous Programming: Using asynchronous operations and callbacks or promises to handle I/O-bound tasks without blocking the main thread. This is widely used in JavaScript and Node.js, and increasingly in other languages.
- Actors and Message Passing: Utilizing a model where independent actors communicate through message passing, allowing for highly concurrent and fault-tolerant systems (e.g., Erlang, Akka).
- Synchronization Primitives: Using tools like mutexes, semaphores, and condition variables to coordinate access to shared resources and prevent race conditions. This is crucial when multiple threads share data.
- Concurrent Data Structures: Employing data structures specifically designed for concurrent access, minimizing the need for explicit synchronization (e.g., ConcurrentHashMap in Java).
Example (Java with threads):
ExecutorService executor = Executors.newFixedThreadPool(10); // Thread pool with 10 threads for (int i = 0; i < 100; i++) { executor.submit(() -> { // Submit a task to the thread pool // Perform some computation }); } executor.shutdown();The choice of concurrency strategy depends on the specific requirements of the application. Thorough consideration of factors like performance, scalability, and maintainability is essential.
Q 7. Explain the difference between HTTP and HTTPS.
Both HTTP and HTTPS are protocols used for communication over the internet, but HTTPS provides an additional layer of security.
HTTP (Hypertext Transfer Protocol) is the foundation of data communication on the World Wide Web. It’s an unencrypted protocol, meaning that data transmitted using HTTP can be intercepted and viewed by third parties. Think of sending a postcard – anyone can read it.
HTTPS (Hypertext Transfer Protocol Secure) is an extension of HTTP that uses SSL/TLS (Secure Sockets Layer/Transport Layer Security) to encrypt the communication between the client (e.g., web browser) and the server. This encryption protects the data from eavesdropping and tampering. Think of sending a letter in a sealed envelope – only the intended recipient can read it.
Key Differences:
- Security: HTTPS encrypts data; HTTP does not.
- Port: HTTPS typically uses port 443; HTTP uses port 80.
- Certificate: HTTPS requires an SSL/TLS certificate to establish a secure connection.
Using HTTPS is crucial for applications that handle sensitive data, such as online banking or e-commerce. The padlock icon in the browser address bar indicates a secure HTTPS connection.
Q 8. What is the difference between a stack and a queue?
Stacks and queues are both fundamental data structures used to store and manage collections of elements, but they differ significantly in how elements are added and removed.
A stack follows the Last-In, First-Out (LIFO) principle. Imagine a stack of plates – you can only add a new plate to the top, and you can only remove the plate from the top. The last plate you put on is the first one you take off.
- Push operation: Adds an element to the top of the stack.
- Pop operation: Removes and returns the element from the top of the stack.
A queue, on the other hand, follows the First-In, First-Out (FIFO) principle. Think of a queue at a store – the first person in line is the first person served.
- Enqueue operation: Adds an element to the rear of the queue.
- Dequeue operation: Removes and returns the element from the front of the queue.
Real-world examples: Stacks are used in function call stacks (managing function calls and their local variables), undo/redo functionality in applications, and expression evaluation. Queues are used in managing tasks in operating systems, handling print jobs, and implementing breadth-first search algorithms.
Q 9. What are some common design patterns you have used?
Throughout my career, I’ve utilized several design patterns extensively, adapting them to various project needs. Some of the most common ones include:
- Singleton Pattern: Ensures that only one instance of a class is created and provides a global point of access to it. This is incredibly useful for managing resources like database connections or logging services, preventing conflicts and ensuring consistent behavior. For instance, in a game, you might have a single instance of a ‘Game Manager’ class to control the game state.
- Factory Pattern: Provides an interface for creating objects without specifying the exact class of object that will be created. This promotes loose coupling and allows for easy addition of new object types without modifying existing code. I’ve used this extensively in building configuration systems where the type of configuration object could vary based on environment settings.
- Observer Pattern: Defines a one-to-many dependency between objects so that when one object changes state, all its dependents are notified and updated automatically. This is invaluable for building event-driven systems like user interfaces, where updates to a model automatically reflect in the view.
- MVC (Model-View-Controller): A widely used architectural pattern that separates concerns into three interconnected parts: the model (data and business logic), the view (user interface), and the controller (managing user input and updates to the model). I’ve used MVC to build several web applications, separating concerns for better maintainability and testability.
The choice of pattern always depends on the specific problem at hand and the project’s overall architecture. A well-chosen pattern can significantly improve code quality, maintainability, and scalability.
Q 10. Explain the concept of polymorphism.
Polymorphism, meaning ‘many forms,’ is a powerful object-oriented programming concept that allows objects of different classes to be treated as objects of a common type. This is achieved through inheritance and interfaces.
Consider a scenario where you have a base class Animal with a method makeSound(). Different animal classes like Dog, Cat, and Bird inherit from Animal and implement their own versions of makeSound(). This allows you to have an array of Animal objects containing instances of Dog, Cat, and Bird. When you call makeSound() on each element, you’ll get the appropriate sound for each animal, demonstrating polymorphism.
class Animal {
makeSound() { console.log('Generic animal sound'); }
}
class Dog extends Animal {
makeSound() { console.log('Woof!'); }
}
class Cat extends Animal {
makeSound() { console.log('Meow!'); }
}
let animals = [new Dog(), new Cat(), new Animal()];
animals.forEach(animal => animal.makeSound());
This allows for flexible and extensible code, as you can add new animal types without modifying existing code.
Q 11. Describe your experience with version control systems (e.g., Git).
Git is an indispensable part of my workflow. I’ve used it extensively for managing codebases of varying sizes and complexities, from personal projects to large-scale enterprise applications. My experience spans all aspects of Git, including:
- Version control: Tracking changes, managing branches, merging code, and resolving conflicts.
- Collaboration: Working with teams on shared repositories, using pull requests and code reviews.
- Branching strategies: Utilizing feature branches, release branches, and other branching models to manage different versions and features concurrently. I’m proficient with Gitflow and other similar workflows.
- Remote repositories: Working with platforms like GitHub, GitLab, and Bitbucket to host and manage code repositories.
- Command-line proficiency: While I use GUI tools for some tasks, I’m comfortable using the command line for more complex scenarios and scripting automation.
I’ve used Git to effectively manage large codebases, facilitating collaboration and streamlining the development process. Understanding Git’s branching model and conflict resolution strategies has been crucial in preventing problems and ensuring smooth team collaboration.
Q 12. How do you debug complex software issues?
Debugging complex software issues requires a systematic approach. My process typically involves:
- Reproduce the problem: The first step is to consistently reproduce the bug. This often involves collecting detailed error messages, logs, and input data that lead to the issue.
- Isolate the problem: Once reproduced, I try to isolate the root cause. This might involve using logging statements, breakpoints in the debugger, or progressively simplifying the input data.
- Use debugging tools: Debuggers, profilers, and logging frameworks are invaluable for identifying the exact point of failure and analyzing the program’s execution flow. I use techniques like stepping through code line by line, inspecting variables, and observing the call stack.
- Analyze code and data: Carefully examining the code and data structures involved in the problem is critical. I often use code review techniques to understand the logic flow and potential areas of error.
- Test potential solutions: Once I’ve identified a potential fix, I conduct thorough testing to validate that the issue has been resolved and that it hasn’t introduced new problems.
- Document the solution: For complex issues, I document the bug, my debugging process, and the solution for future reference and to prevent similar issues from recurring.
Often, debugging requires a blend of technical skills and problem-solving aptitude. It’s a process of systematic investigation, and experience helps significantly in narrowing down potential causes and choosing effective debugging strategies.
Q 13. What are your preferred testing methodologies?
My preferred testing methodologies are guided by the principles of comprehensive test coverage and maintainability. I typically use a combination of the following:
- Unit testing: Testing individual components or modules in isolation. I leverage frameworks like JUnit or pytest to write automated unit tests, ensuring each part functions correctly.
- Integration testing: Testing the interaction between different modules to verify that they work together as expected. This helps catch integration-related issues that might not be apparent in unit tests.
- System testing: Testing the entire system as a whole to ensure it meets requirements. This often involves manual testing, but automated tests can also be used where possible.
- Regression testing: Retesting the system after changes or bug fixes to ensure that existing functionality hasn’t been broken. This is a crucial step for maintaining stability and preventing regressions.
- Test-driven development (TDD): I often use TDD where appropriate, writing tests before writing the actual code. This helps to clarify requirements and guides the design process.
The specific testing approach adapts to the project’s scale and complexity. For example, in smaller projects, less formal testing might suffice, while large enterprise systems often require more rigorous and comprehensive testing practices.
Q 14. Explain the difference between SQL and NoSQL databases.
SQL and NoSQL databases represent fundamentally different approaches to data management. The key distinctions lie in their data model, query language, and scalability characteristics.
SQL databases (relational databases) organize data into tables with rows and columns, enforcing relationships between tables through constraints. They use SQL (Structured Query Language) for querying and manipulating data, providing a standardized and robust approach to data management. They are highly structured and offer ACID properties (Atomicity, Consistency, Isolation, Durability) ensuring data integrity. Examples include MySQL, PostgreSQL, and Oracle.
NoSQL databases (non-relational databases) offer more flexible data models, often using key-value stores, document stores, graph databases, or wide-column stores. They are designed to handle large volumes of unstructured or semi-structured data and offer high scalability and availability. They often prioritize availability and partition tolerance over consistency (CAP theorem). Examples include MongoDB, Cassandra, Redis, and Neo4j.
Choosing between SQL and NoSQL: The choice often depends on the application’s specific needs. SQL databases are better suited for applications requiring strong data integrity and complex queries, while NoSQL databases excel in handling large volumes of unstructured data, high write loads, and distributed environments. Sometimes, a hybrid approach using both SQL and NoSQL databases is the optimal solution.
Q 15. What is your experience with cloud computing platforms (AWS, Azure, GCP)?
My experience with cloud computing platforms spans several years and encompasses AWS, Azure, and GCP. I’ve worked extensively on AWS, leveraging services like EC2 for compute, S3 for storage, and RDS for databases. I’ve built and deployed numerous applications using these services, focusing on scalability, reliability, and cost optimization. For example, I designed a microservices architecture on AWS using ECS and EKS, ensuring high availability through load balancing and auto-scaling. With Azure, I’ve utilized Azure Functions for serverless computing and Azure Blob Storage for efficient data management, mainly focusing on projects requiring strong integration with other Microsoft products. My GCP experience includes utilizing Compute Engine and Cloud SQL, primarily for projects demanding advanced data analytics capabilities and leveraging Google’s machine learning APIs. I’m comfortable with the core concepts of each platform, including networking, security, and identity management. I understand the strengths and weaknesses of each provider and can select the most appropriate platform based on project requirements.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. How do you optimize database queries for performance?
Optimizing database queries for performance involves a multi-faceted approach. It’s like streamlining a busy highway—you need to identify bottlenecks and optimize the flow. First, I analyze the query execution plan using tools like EXPLAIN (for MySQL) or similar features provided by the database system. This reveals where the query spends most of its time. Common issues include missing indexes, inefficient joins, and unnecessary table scans. Then, I address these issues: I add indexes to frequently queried columns, ensuring they’re the right type (B-tree, hash, etc.) for the operation. I optimize joins by using appropriate join types (INNER JOIN, LEFT JOIN, etc.) and ensuring tables are correctly indexed. I rewrite queries to reduce the number of operations, utilizing subqueries efficiently and avoiding unnecessary calculations. For example, instead of fetching all data and then filtering in application code, I perform the filtering within the database using WHERE clauses. Finally, I regularly review query performance and identify areas for ongoing improvement. Profiling tools and monitoring database metrics are critical to this process. Imagine it like constantly monitoring traffic flow on that highway and adjusting traffic lights to optimize throughput.
Q 17. What are some common security vulnerabilities and how do you mitigate them?
Common security vulnerabilities are numerous, but some of the most prevalent include SQL injection, cross-site scripting (XSS), and cross-site request forgery (CSRF). SQL injection attacks exploit vulnerabilities in how applications handle user inputs. Mitigation involves parameterized queries or prepared statements, which treat user input as data rather than executable code. XSS attacks inject malicious scripts into websites. Mitigation includes proper input sanitization and output encoding, preventing the execution of untrusted scripts. CSRF attacks trick users into performing unwanted actions. Mitigation includes using CSRF tokens, which validate the authenticity of requests. Beyond these, secure coding practices are crucial. This includes regularly updating software and libraries, validating all user inputs, implementing input validation and sanitization, and employing robust authentication and authorization mechanisms. Regularly performing security audits and penetration testing helps identify weaknesses in a system’s security posture. Think of it like building a house—you wouldn’t skip steps like proper foundation or lock installation; you need a layered security approach for comprehensive protection.
Q 18. Describe your experience with different data structures (arrays, linked lists, trees, graphs).
My experience with data structures is extensive. I’ve utilized arrays for their efficient random access, but I’m aware of their limitations when it comes to insertions and deletions. Linked lists offer advantages for dynamic data where insertions and deletions are frequent, particularly in scenarios such as managing a queue or stack. Trees, especially binary search trees and AVL trees, provide efficient searching, insertion, and deletion operations—I’ve used them extensively in implementing algorithms like sorting and searching. Graphs are essential for representing relationships between data points. I’ve applied graph algorithms, such as Dijkstra’s algorithm and breadth-first search, for tasks like finding the shortest path in a network or identifying connected components. Choosing the right data structure depends heavily on the specific problem and the required operations. Each data structure comes with its own performance characteristics (time and space complexity) which I carefully consider while selecting the best fit for the application.
Q 19. Explain the concept of Big O notation.
Big O notation describes the upper bound of the time or space complexity of an algorithm as the input size grows. It’s a way to classify algorithms based on their efficiency. For example, O(n) represents linear time complexity—the runtime increases linearly with the input size (e.g., searching an unsorted array). O(log n) represents logarithmic time complexity—the runtime increases logarithmically with the input size (e.g., searching a sorted array using binary search). O(n^2) represents quadratic time complexity—the runtime increases quadratically with the input size (e.g., bubble sort). O(1) represents constant time complexity—the runtime remains constant regardless of the input size (e.g., accessing an element in an array using its index). Big O notation helps developers compare the efficiency of different algorithms and choose the most suitable one for a given task. It is crucial for building scalable and performant software.
Q 20. How do you handle exceptions in your code?
Exception handling is crucial for robust code. My approach involves using try-catch blocks (or equivalent constructs in other languages) to gracefully handle potential errors. Instead of letting exceptions terminate the program abruptly, I capture them and implement appropriate recovery mechanisms. For example, I might log the error, display a user-friendly message, or attempt an alternative solution. Choosing the right exception type is essential—this ensures that the correct error handling logic is executed. I avoid using bare catch blocks, as they mask errors that might not be handled appropriately. Instead, I catch specific exception types to ensure precise handling. I frequently use custom exception classes to represent specific error conditions within my application, improving code clarity and maintainability. Exception handling is crucial not only for reliability but also for security to prevent information leakage through error messages. A robust exception handling strategy prevents application crashes and ensures a better user experience.
Q 21. What is your experience with different programming languages?
My experience includes proficiency in several programming languages. I’m highly proficient in Java, utilizing its object-oriented features and vast libraries for building large-scale applications. I’m also skilled in Python, leveraging its versatility for data science, scripting, and rapid prototyping. My experience with C++ allows me to develop high-performance applications where memory management and control are crucial. I’m also familiar with JavaScript, primarily for front-end web development, and have experience with other languages like Go and SQL as needed for specific tasks. My choice of language is dictated by the project’s specific requirements, considering factors like performance needs, development speed, and available libraries.
Q 22. Describe a time you had to solve a difficult technical problem.
One particularly challenging problem involved optimizing the performance of a high-traffic e-commerce website. The application was experiencing significant slowdowns during peak hours, impacting user experience and sales. Initially, we suspected database queries were the bottleneck. However, after profiling the application using tools like New Relic and tracing individual requests, we discovered the real culprit was inefficient image processing. We were using a legacy image resizing library that wasn’t optimized for the volume of requests.
My approach involved a multi-pronged strategy. First, we identified and isolated the specific image processing functions consuming the most resources. Then, we benchmarked several alternative libraries, including sharp and ImageMagick. We chose ImageMagick, given its superior performance in our tests and its ability to leverage multi-core processing. We implemented a caching mechanism using Redis to store resized images, significantly reducing the load on the image processing servers. Finally, we implemented robust logging and monitoring to track performance improvements and detect future bottlenecks. The result was a 70% reduction in page load time during peak hours, leading to a measurable increase in conversion rates.
Q 23. Explain your approach to designing a scalable system.
Designing a scalable system requires careful consideration of several key architectural principles. Think of it like building a house: you wouldn’t start constructing the roof before laying a solid foundation. Similarly, scalable systems need a strong base. My approach typically involves:
- Microservices Architecture: Breaking down the application into smaller, independent services that can be scaled individually. This allows us to scale only the parts that need it, optimizing resource utilization. For example, the user authentication service might require more resources than the product catalog service.
- Horizontal Scaling: Adding more servers to handle increased load instead of relying on vertical scaling (upgrading individual servers). This is cheaper and more flexible.
- Load Balancing: Distributing traffic across multiple servers to prevent overload on any single server. Think of this as having multiple cashiers to handle customers at a store instead of just one.
- Caching: Storing frequently accessed data in a fast, readily available memory space (like Redis or Memcached) to reduce database load. This is like keeping frequently used items readily accessible in a retail store.
- Asynchronous Processing: Handling non-critical tasks (like sending emails or processing images) asynchronously using message queues (like RabbitMQ or Kafka) to improve responsiveness.
- Database Optimization: Using appropriate database technologies and optimizing queries to ensure database performance keeps up with application scaling. This could involve using NoSQL databases for specific parts of the application.
Throughout this process, I emphasize robust monitoring and logging to identify bottlenecks and track the system’s overall performance. Regular load testing is crucial to ensure the system can handle anticipated growth.
Q 24. How do you ensure code quality and maintainability?
Ensuring code quality and maintainability is paramount. It’s like building a house—you want it to be strong, functional, and easy to repair or renovate later. My approach relies on a combination of practices:
- Code Reviews: Having other developers review my code helps catch bugs, inconsistencies, and improve overall code style. It’s a crucial process to ensure the consistency of our coding practices.
- Static Code Analysis: Using tools like SonarQube or ESLint to automatically detect potential issues such as bugs, vulnerabilities, and code style violations before they reach production.
- Unit Testing: Writing unit tests to ensure individual components of the application function correctly. This helps to prevent regressions when making changes.
- Integration Testing: Testing how different parts of the application interact with each other. This verifies that individual components function correctly as a cohesive unit.
- Following Coding Standards: Adhering to consistent coding style and conventions to improve readability and maintainability. This is akin to following architectural blueprints in construction.
- Documentation: Writing clear and concise documentation for both the code and the application. This makes it easier for others (and my future self!) to understand and maintain the code.
By consistently applying these techniques, we can create a higher-quality, more maintainable codebase.
Q 25. What is your experience with continuous integration/continuous deployment (CI/CD)?
I have extensive experience with CI/CD pipelines, using tools like Jenkins, GitLab CI, and Azure DevOps. My experience encompasses the entire lifecycle, from code commits to deployment to various environments (development, testing, staging, production). A typical CI/CD pipeline I’ve worked with includes:
- Version Control (Git): Using Git for code management and collaboration.
- Automated Builds: Automatically building the application whenever code is committed.
- Automated Testing: Running unit, integration, and possibly end-to-end tests automatically to ensure code quality.
- Deployment Automation: Automatically deploying the application to different environments using tools like Docker and Kubernetes.
- Monitoring and Logging: Implementing robust monitoring and logging to track the health and performance of the deployed application.
In a recent project, we leveraged a GitLab CI/CD pipeline to implement a blue/green deployment strategy, minimizing downtime during deployments. This approach ensures that there is always a live and functional version of the application running before new features are launched. This reduced deployment risks significantly.
Q 26. Explain the concept of refactoring.
Refactoring is the process of restructuring existing computer code without changing its external behavior. It’s like renovating a house—you’re not changing the overall layout or purpose, but you’re improving its internal structure and functionality. The goal is to improve code quality, readability, and maintainability. This involves techniques such as:
- Simplifying Complex Code: Breaking down large, convoluted functions into smaller, more manageable ones.
- Improving Code Structure: Reorganizing code to enhance readability and clarity.
- Removing Duplicated Code: Extracting common code into reusable functions or classes.
- Renaming Variables and Functions: Using more descriptive and meaningful names to improve understanding.
- Improving Code Style: Ensuring consistency with coding standards.
Refactoring should always be done in small, incremental steps, with thorough testing at each stage to avoid introducing bugs. A common refactoring technique I use is extracting methods to create more modular and testable code. For example, a long function that performs multiple tasks could be broken into several smaller, more focused functions. This improves the maintainability and testability of the codebase.
Q 27. How do you stay up-to-date with the latest technologies?
Staying up-to-date with the latest technologies is crucial in software engineering. It’s a continuous learning journey. My strategies include:
- Following Industry Blogs and Publications: Regularly reading blogs and articles from reputable sources such as InfoQ, DZone, and Martin Fowler’s blog.
- Attending Conferences and Workshops: Participating in industry conferences and workshops to learn about new technologies and best practices from experts.
- Online Courses and Tutorials: Taking online courses and tutorials on platforms like Coursera, Udemy, and Pluralsight to deepen my knowledge in specific areas.
- Contributing to Open Source Projects: Contributing to open-source projects provides hands-on experience with new technologies and allows me to learn from experienced developers.
- Experimenting with New Tools and Technologies: Experimenting with new tools and technologies in personal projects to gain practical experience.
By actively engaging in these activities, I can stay ahead of the curve and adapt to the ever-evolving landscape of software development.
Q 28. What are your salary expectations?
My salary expectations are in line with the market rate for a software engineer with my experience and skill set in this area. I’m confident that my contributions will quickly add significant value to your team. I am open to discussing specific compensation details further based on the full scope of the role and responsibilities.
Key Topics to Learn for SWE Interview
- Data Structures and Algorithms: Understanding fundamental data structures like arrays, linked lists, trees, graphs, and hash tables is crucial. Practical application includes optimizing code for speed and memory efficiency in various scenarios.
- Object-Oriented Programming (OOP): Master the principles of encapsulation, inheritance, and polymorphism. Apply OOP concepts to design robust and maintainable software systems. Explore design patterns for common programming problems.
- System Design: Learn to design scalable and reliable systems, considering factors like database choices, API design, and load balancing. Practice designing systems for specific use cases, focusing on trade-offs and efficient solutions.
- Databases: Familiarize yourself with relational (SQL) and NoSQL databases. Understand database design principles, query optimization, and transaction management. Practice writing efficient SQL queries and understand the strengths and weaknesses of different database technologies.
- Software Testing and Debugging: Develop strong debugging skills and understand different testing methodologies (unit, integration, system testing). Learn how to write effective test cases and identify potential issues in your code.
- Coding Proficiency: Practice coding in at least one popular language (e.g., Java, Python, C++, JavaScript). Focus on writing clean, readable, and efficient code. Be prepared to solve coding challenges efficiently and explain your thought process clearly.
Next Steps
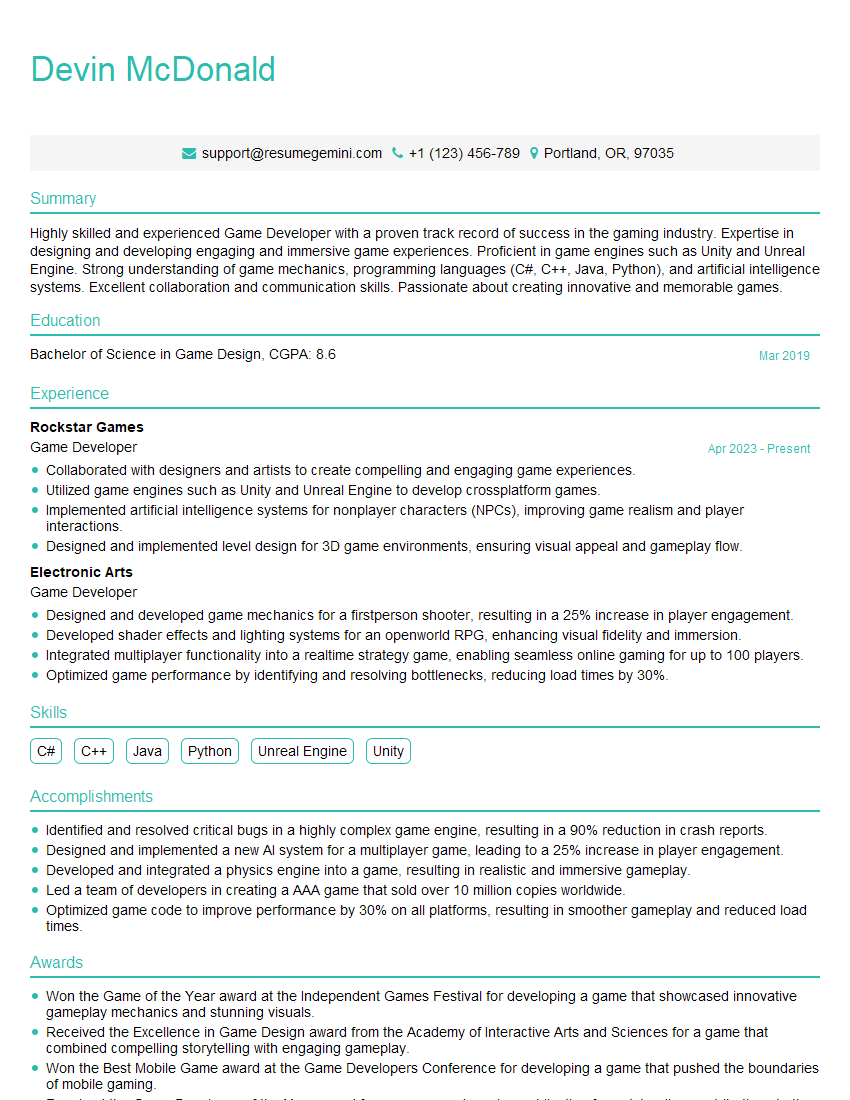
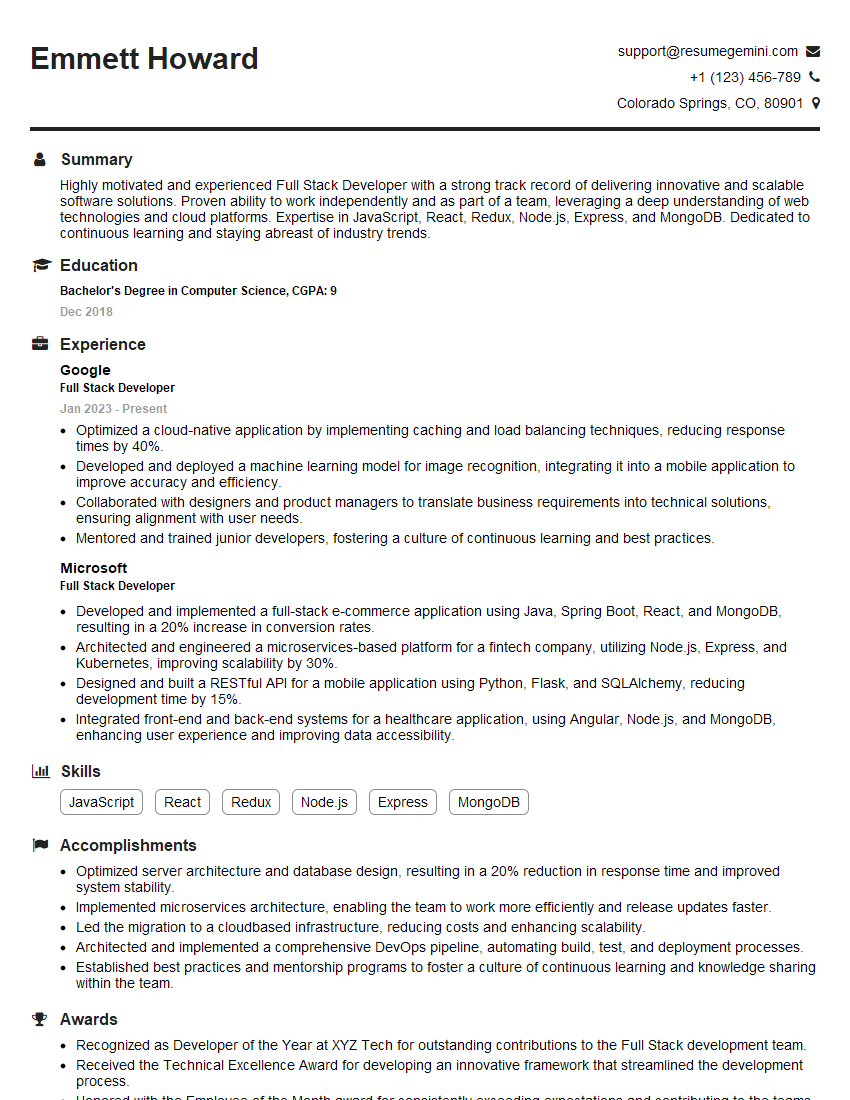
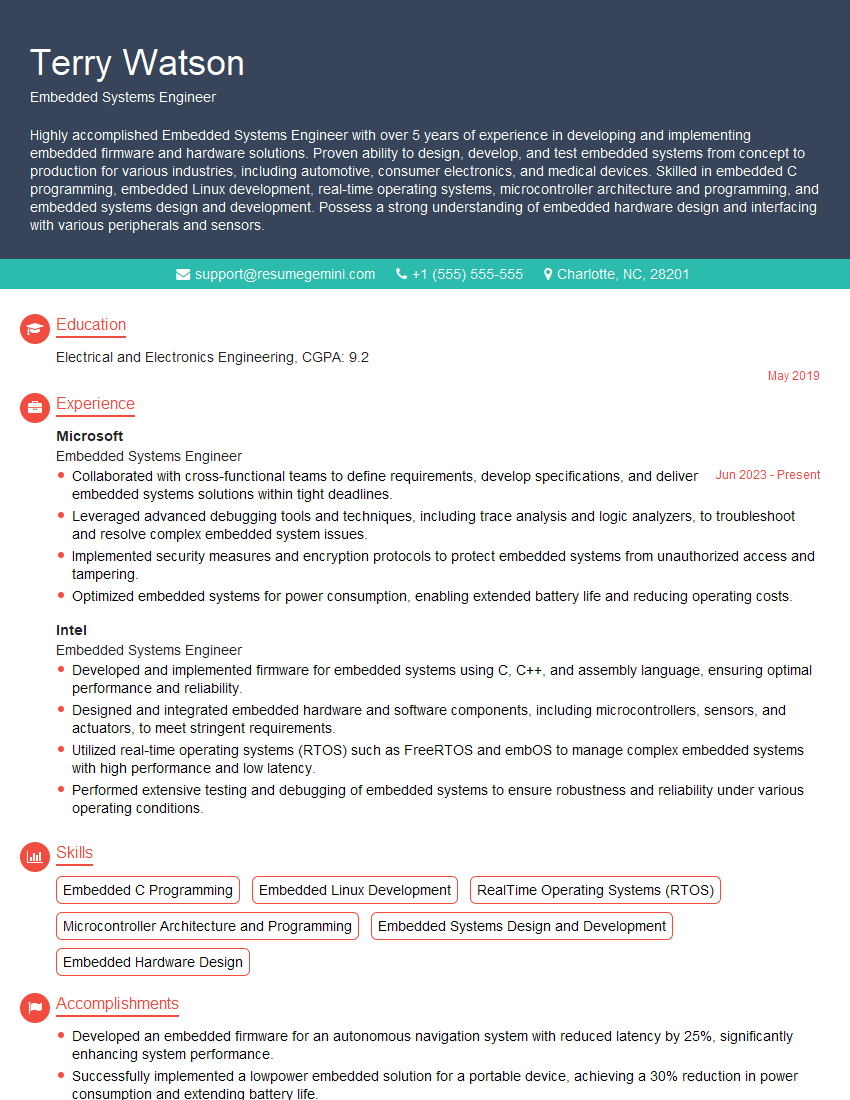
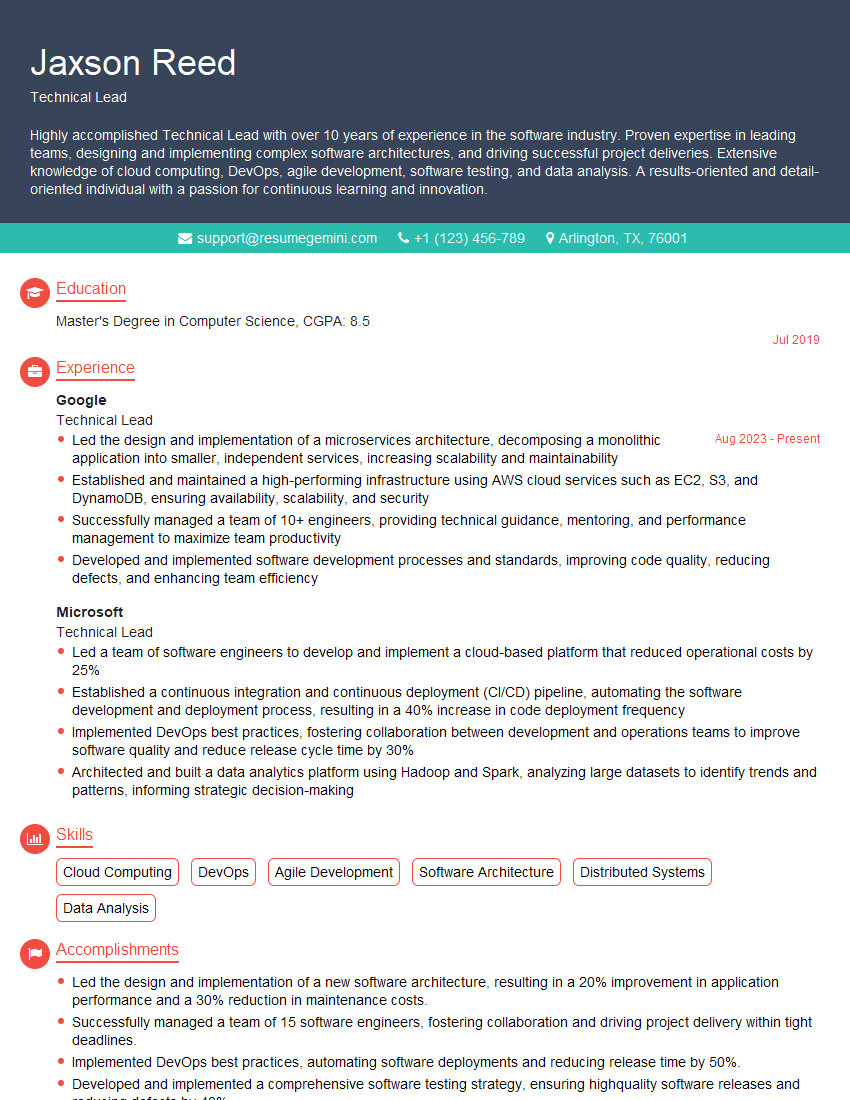
Mastering Software Engineering principles is key to unlocking exciting career opportunities and achieving your professional goals. A strong foundation in these areas will significantly enhance your job prospects and open doors to challenging and rewarding roles. To maximize your chances of landing your dream job, create an ATS-friendly resume that highlights your skills and experience effectively. ResumeGemini is a trusted resource to help you build a professional and impactful resume. We provide examples of resumes tailored specifically for Software Engineering roles to help you get started.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Amazing blog
hello,
Our consultant firm based in the USA and our client are interested in your products.
Could you provide your company brochure and respond from your official email id (if different from the current in use), so i can send you the client’s requirement.
Payment before production.
I await your answer.
Regards,
MrSmith
hello,
Our consultant firm based in the USA and our client are interested in your products.
Could you provide your company brochure and respond from your official email id (if different from the current in use), so i can send you the client’s requirement.
Payment before production.
I await your answer.
Regards,
MrSmith
These apartments are so amazing, posting them online would break the algorithm.
https://bit.ly/Lovely2BedsApartmentHudsonYards
Reach out at BENSON@LONDONFOSTER.COM and let’s get started!
Take a look at this stunning 2-bedroom apartment perfectly situated NYC’s coveted Hudson Yards!
https://bit.ly/Lovely2BedsApartmentHudsonYards
Live Rent Free!
https://bit.ly/LiveRentFREE
Interesting Article, I liked the depth of knowledge you’ve shared.
Helpful, thanks for sharing.
Hi, I represent a social media marketing agency and liked your blog
Hi, I represent an SEO company that specialises in getting you AI citations and higher rankings on Google. I’d like to offer you a 100% free SEO audit for your website. Would you be interested?